Executive Summary: Fake computer virus warnings — also known as scareware or rogue security alerts — are one of the most pervasive and psychologically manipulative threats facing PC users today. These deceptive pop-ups, emails, and system tray mimics are engineered not to protect you, but to panic you into downloading malware, surrendering payment details, or granting remote access to cybercriminals. This comprehensive guide will teach you exactly how to identify a fake virus popup versus a legitimate alert, what immediate steps to take when you encounter one, how to fortify your defenses with trusted real-time protection like 360 Total Security, and how to recognize the broader ecosystem of tech support scams that exploit the same vulnerabilities. Whether you are a casual browser or a seasoned professional, understanding these threats is your first and most powerful line of defense.
What Are Fake Computer Virus Warnings?
Fake virus warnings are deceptive pop-ups, browser alerts, or system notifications that are not generated by any legitimate antivirus software installed on your machine. They are crafted by cybercriminals and distributed through malicious websites, compromised ad networks, phishing emails, and bundled software installers. Their singular goal is to trick you into performing a harmful action — clicking a dangerous link, downloading rogue software, or paying for a fraudulent service. Unlike genuine security alerts, which inform and guide, fake warnings are designed to destabilize and manipulate.
Common Forms of Fake Security Alerts
Understanding the delivery mechanisms of fake security alerts is the first step toward immunity. These scams manifest in several distinct but equally dangerous forms:
- Browser-based pop-up windows: These appear suddenly while you are browsing a website — often one you have never visited before — claiming your computer is critically infected and demanding immediate action. They frequently use full-screen overlays or audio alerts to amplify the sense of emergency.
- Email warnings with fabricated scan results: A carefully crafted email arrives in your inbox, complete with official-looking logos, claiming a recent scan of your system detected dangerous threats. It includes a link to download a “security patch” or “removal tool” — which is, in reality, malware.
- System tray icon mimics: Perhaps the most insidious form, these involve rogue software that has already been installed (often bundled with a free download) and places a blinking red icon in your Windows system tray, mimicking the appearance of a real antivirus program like Windows Defender or a well-known security suite.

The Psychology Behind These Scams
The effectiveness of fake virus warnings is not accidental — it is the result of deliberate psychological engineering. According to a 2026 Cybersecurity Threat Intelligence Report analyzing social engineering tactics, scareware campaigns consistently exploit three core psychological levers:
- Fear and urgency: By presenting a manufactured crisis with a ticking clock (“Your computer will be disabled in 5 minutes!”), scammers short-circuit rational thinking. When people are afraid, they act impulsively rather than analytically — exactly what the attacker wants.
- Perceived legitimacy: Fake alerts invest heavily in visual authenticity. They replicate the logos, color schemes, and technical terminology of trusted brands like Microsoft, Norton, or McAfee. A warning that looks professional feels credible, especially to users who may not regularly interact with their real security software.
- Exploitation of technical knowledge gaps: The average PC user is not a cybersecurity expert. Scammers exploit this by using intimidating jargon — “registry corruption”, “kernel-level intrusion”, “rootkit detected” — to create confusion and dependency. When users feel out of their depth, they are far more likely to defer to the “authority” of the fake warning.
Why Fake Warnings Are a Major Threat
The consequences of interacting with a fake virus warning extend far beyond a wasted afternoon. These scams represent a genuine and escalating cybersecurity threat for several critical reasons:
- Direct malware installation: Clicking any button within a fake warning — even “Scan Now”, “Remove Threats”, or “Protect My PC” — can trigger the download and silent installation of actual malware, including spyware, ransomware, or adware.
- Financial theft: Many fake warnings culminate in a payment screen for a “full version” of their bogus security software. Victims who enter their credit card details hand that financial information directly to criminals.
- Harmful user actions: In a state of panic, users may follow the fake warning’s instructions to delete files, disable their real antivirus, or grant remote access — actions that cause real, lasting damage to their system and data security.
How Can I Spot a Fake Virus Warning?
Distinguishing a fake alert from a legitimate one is a learnable skill, and once you know what to look for, the differences become unmistakable. Legitimate antivirus software like 360 Total Security follows consistent, transparent, and non-pressuring communication patterns. Fake warnings, by contrast, are characterized by aggression, vagueness, and impossible demands. Here is how to apply a systematic lens to any security alert you encounter.
Source and Context: The First Clue
The most fundamental question to ask when you see a security alert is: where is this coming from?
- Legitimate alerts originate from your installed software: A real antivirus notification will appear as a notification from the program you have installed and can verify in your applications list. It will not materialize out of nowhere inside a web browser window from a website you just visited.
- Context matters enormously: If you are browsing a file-sharing site, a streaming platform with aggressive ads, or an unfamiliar domain, and a security warning suddenly fills your screen, treat it as a scam by default. Your browser does not have the capability to scan your hard drive — any warning claiming it has done so is categorically false.
Language and Design: Analyzing the Message
Once you have assessed the source, examine the message itself with a critical eye. The language and visual design of a security alert reveal its true nature almost immediately.
- Fake warnings use extreme, vague, emotional language: Phrases like “CRITICAL INFECTION DETECTED!”, “YOUR PERSONAL DATA IS BEING STOLEN RIGHT NOW!”, or “IMMEDIATE ACTION REQUIRED OR YOUR PC WILL BE DESTROYED!” are hallmarks of scareware. The goal is to overwhelm your judgment, not inform it.
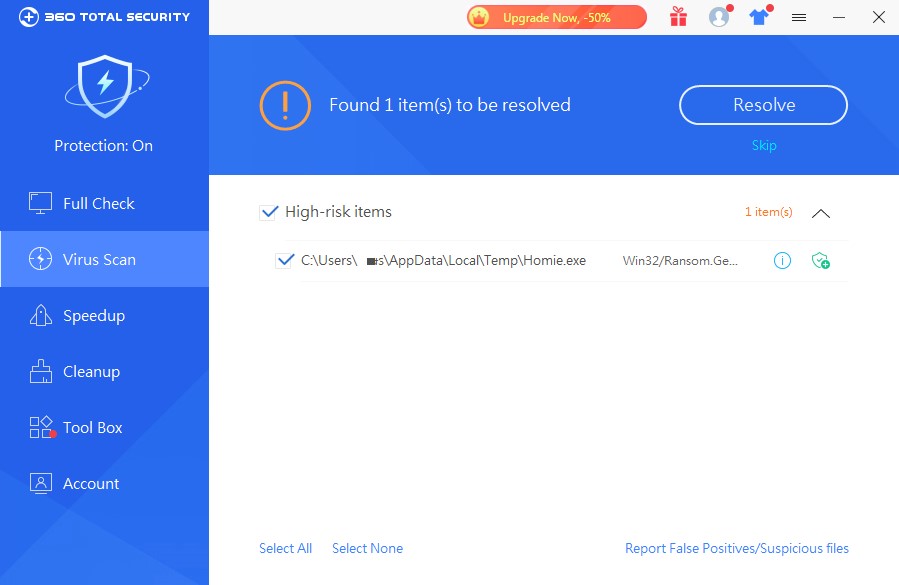
- Real alerts are specific, factual, and calm: A genuine notification from 360 Total Security, for example, will identify the specific threat by name (e.g., “Trojan.Generic.KD.12345 detected in C:\Users\Downloads\setup.exe”), explain what it does, and present clear options — typically to quarantine or remove the file — without demanding payment or creating a crisis atmosphere.
- Look for linguistic red flags: Poor grammar, spelling errors, awkward phrasing, and generic company names like “PC Security Center”, “Windows Protection Suite”, or “Online Shield Pro” are strong indicators of a scam. Legitimate software companies employ professional content teams and undergo rigorous quality control.

Behavior and Requests: The Ultimate Test
If you are still uncertain after evaluating source and language, the behavior of the alert will remove all doubt. Fake warnings have behavioral signatures that legitimate software never exhibits:
- They resist closure: A fake warning may disable the “X” close button, reopen immediately after you close it, or use browser dialog loops that make it appear you cannot leave the page. This is a manipulation tactic, not a security feature.
- They demand payment to remove threats: No reputable antivirus program — including free-tier versions of 360 Total Security — will ask for your credit card number as a prerequisite to removing a detected threat. If a warning demands payment upfront to “clean” your system, it is a scam, without exception.
- They ask for remote access: Some advanced scams escalate by providing a phone number and asking you to allow a “technician” to connect to your PC remotely. This grants attackers direct, unrestricted access to your files, accounts, and system settings.
What Immediate Actions Should I Take?
Encountering a fake virus warning can be a disorienting experience, but having a clear, pre-planned response protocol transforms a moment of potential panic into a controlled, safe procedure. The cardinal rule is simple: do not engage with the warning on its own terms. Here is your step-by-step action plan.
Step 1: Safe Closure Without Engagement
Your immediate priority is to close the fake warning without clicking anything inside it. Here is how to do it safely:
- Close the browser tab or window: If the fake warning is browser-based, try closing the specific tab first. If the tab is unresponsive or the warning prevents you from navigating away, close the entire browser window.
- Use Task Manager for persistent pop-ups: If the browser window itself is frozen or the pop-up keeps reappearing, press Ctrl + Shift + Esc to open Windows Task Manager. Find your browser process (e.g., “Chrome”, “Edge”, “Firefox”) in the list, right-click it, and select “End Task”. This force-closes the browser without you having to interact with the scam page.
# To force-close a frozen browser via Task Manager:
# 1. Press Ctrl + Shift + Esc
# 2. Navigate to the "Processes" tab
# 3. Find your browser (e.g., chrome.exe, msedge.exe, firefox.exe)
# 4. Right-click > "End Task"
# Note: You will lose any unsaved browser sessions, but this is a safe trade-off.Critical reminder: Never click “Scan Now”, “Remove Virus”, “Protect My PC”, “Buy Now”, or any other button displayed within the fake warning. Even the “Close” or “Cancel” button inside the fake dialog can trigger a malicious download.
Step 2: Initiate a Scan with Trusted Software
Once the fake warning is closed, your next priority is to verify that your system has not already been compromised — either by the site that served the fake warning or by previously installed rogue software.
- Open your legitimate, installed antivirus program: Launch it directly from your Start Menu or desktop shortcut — not from any link provided in the warning. If you do not currently have a reputable antivirus solution installed, download 360 Total Security directly from its official website. It offers a comprehensive free version with robust malware detection capabilities.
- Run a full system scan: Do not settle for a quick scan in this situation. Run a full or deep system scan to examine every file, process, and registry entry. This ensures that any malware that may have silently installed itself alongside the fake warning is detected and flagged.
Step 3: Post-Scan Cleanup and Verification
After your scan completes, follow through with a thorough cleanup to ensure the threat is fully neutralized and cannot resurface.
- Follow your antivirus’s remediation guidance: 360 Total Security presents detected threats in a clear, organized interface with straightforward options to quarantine or permanently remove each item. Follow these instructions carefully and do not dismiss threats without acting on them.
- Clear your browser cache and cookies: Malicious scripts that trigger fake pop-ups can persist in your browser cache. Clearing it removes these scripts and prevents the fake warning from reappearing the next time you browse. In most browsers, you can do this via Settings > Privacy > Clear Browsing Data.
- Review recently installed programs: Navigate to Control Panel > Programs > Uninstall a Program and sort by installation date. If you see any unfamiliar programs installed recently — especially around the time you encountered the fake warning — research them before uninstalling, and remove any confirmed rogue software.
Use the following checklist to guide your response every time you encounter a suspicious security alert:
| ✅ DO THIS | ❌ DON’T DO THIS |
|---|---|
| Close the browser tab or use Task Manager to end the browser process | Click any button inside the fake warning (including “Close” or “Cancel”) |
| Open your real, installed antivirus software directly | Download software from a link provided in the warning |
| Run a full system scan with trusted security software | Enter any payment or personal information |
| Clear your browser cache and cookies after the incident | Call any phone number displayed in the warning |
| Review recently installed programs for rogue software | Grant remote access to anyone who contacts you about the warning |
| Report the scam to relevant authorities (e.g., FTC, Action Fraud) | Panic and follow the warning’s instructions without verification |
How Do I Protect Myself from Future Fake Warnings?
Reactive responses are essential, but the most effective strategy against fake virus warnings is a proactive, layered defense that prevents these scams from reaching you in the first place. True protection combines robust software, smart browser configuration, and cultivated browsing habits into a comprehensive security posture.
Employ a Reliable Antivirus with Real-Time Protection
The foundation of any effective defense against scareware and fake warnings is a legitimate, actively maintained antivirus solution running on your PC at all times.
- Real-time scanning is non-negotiable: 360 Total Security provides continuous, real-time scanning that intercepts malicious scripts, blocks connections to known scam websites, and prevents unauthorized downloads before they can execute. This means many fake warning delivery mechanisms are neutralized before you ever see them.
- Proactive defense against rogue software: 360 Total Security’s multi-engine detection architecture — incorporating its own QVM AI engine alongside integration with leading industry engines — is specifically calibrated to identify and block scareware, rogue security software, and adware. According to a 2025 independent evaluation by AV-TEST, solutions leveraging multi-engine AI detection demonstrated significantly higher detection rates for potentially unwanted applications (PUAs) and scareware variants compared to single-engine solutions.
- Keep your antivirus updated: Cybercriminals constantly iterate on their fake warning designs and delivery methods to evade detection. Ensure automatic updates are enabled so your antivirus always has the latest threat signatures and behavioral detection rules.
Fortify Your Web Browser
Your web browser is the primary attack surface for fake virus warnings. Hardening it significantly reduces your exposure:
- Enable built-in pop-up blockers: All major browsers — Chrome, Firefox, Edge, and Safari — include native pop-up blockers. Ensure yours is enabled (Settings > Privacy and Security) and set your overall security level to “Strict” or “Enhanced” where available.
- Use reputable ad-blocking and script-blocking extensions: Extensions like uBlock Origin (available for Chrome, Firefox, and Edge) block the ad networks and malicious scripts that commonly serve fake warning pop-ups. Choose extensions with large, active user bases and transparent open-source code to avoid inadvertently adding risk.
- Avoid high-risk websites: “Free download” sites, software crack repositories, unauthorized streaming platforms, and torrent sites are disproportionately responsible for delivering scareware. These sites monetize through aggressive and often malicious advertising. Avoiding them dramatically reduces your exposure.
Cultivate Safe Browsing Habits
Technology alone cannot protect you completely — your own behavior is a critical security variable. Developing these habits creates a powerful human firewall:
- Never download software from pop-up ads or unsolicited emails: Legitimate software is downloaded from official websites or verified app stores — never from a pop-up that appeared unbidden or an email you did not expect. This single rule eliminates a vast majority of scareware infection vectors.
- Verify website security before entering any information: Always look for “https://” and the padlock icon in your browser’s address bar before entering any personal, financial, or login information. While HTTPS alone does not guarantee a site is safe, its absence is a definitive red flag.
- Stay informed about current scam tactics: The landscape of online scams evolves continuously. Following reputable cybersecurity news sources, official government cybersecurity agencies (such as CISA in the US or the NCSC in the UK), and security blogs keeps you aware of new tactics before you encounter them.
Beyond Pop-ups: Recognizing Related Scams and Threats
Fake virus warnings do not exist in isolation. They are one component of a sprawling ecosystem of tech support scams, fraudulent software schemes, and social engineering attacks that all share the same fundamental strategy: exploit anxiety about technology to extract money or access. Recognizing these related threats is essential for comprehensive self-protection.
The Tech Support Phone Scam
One of the most prevalent and financially damaging scams related to fake virus warnings operates over the telephone:
- How it works: You receive an unsolicited phone call from someone claiming to be a technician from “Microsoft Support”, “Windows Technical Department”, or your “Internet Service Provider”. They claim their systems have detected dangerous viruses or errors on your computer and that they need to help you fix it immediately.
- What they want: The caller will direct you to open legitimate Windows tools like Event Viewer (which always shows some non-critical errors, creating a false sense of alarm) to “prove” your computer is infected. They then ask you to install remote desktop software — giving them direct access to your PC — or demand payment via gift cards, wire transfer, or cryptocurrency for their “service”.
As cybersecurity researcher and social engineering specialist Dr. Mara Chen noted in a 2026 industry analysis: “Vishing — voice phishing — has surged precisely because it bypasses technical defenses entirely and targets the most exploitable vulnerability in any security system: human trust. A convincing caller can achieve in minutes what sophisticated malware might take days to accomplish.” Remember: Microsoft, Apple, and legitimate ISPs do not make unsolicited calls about viruses on your computer. Ever.
Fake Antivirus Renewal and Upgrade Notices
Another sophisticated variant targets users who already have legitimate security software installed — exploiting the trust they have in their real provider:
- The impersonation approach: You receive an email that closely mimics official communications from your antivirus brand — complete with logos, formatting, and sender names designed to look authentic. The email claims your subscription has expired, a critical update is available, or your account requires verification, and provides a link to “renew” or “update”.
- The outcome: Clicking the link takes you to a convincing phishing site designed to capture your payment details, or initiates a download of malware disguised as a software update. Always navigate directly to your antivirus provider’s official website by typing the URL manually — never through email links — to manage your subscription or check for updates.
The Connection to Actual Malware
It is critical to understand that fake warnings are frequently not the end goal — they are the delivery mechanism for genuinely destructive malware. The warning itself is the bait; the malware is the hook.
| Fake Warning Type | Common Malware Delivered | Primary Impact |
|---|---|---|
| Browser lock pop-up (“Your computer has been blocked”) | Ransomware / Locker Malware | System lockout, file encryption, ransom demand |
| Fake scan result with “detected threats” | Spyware / Keylogger | Credential theft, financial data harvesting |
| Fake software update notification | Trojan / Backdoor | Persistent unauthorized system access |
| Fake antivirus download prompt | Rogue Security Software / Adware | System slowdown, persistent pop-ups, payment fraud |
| Tech support scam pop-up with phone number | Remote Access Trojan (RAT) | Full remote system control, data theft |
| Fake browser extension installation prompt | Adware / Browser Hijacker | Search redirection, data tracking, ad injection |
This table underscores why the guidance to never interact with a fake warning is so important. What appears to be an annoying pop-up is frequently the first stage of a multi-phase attack with serious consequences for your privacy, finances, and system integrity. Protecting yourself starts with recognition and is sustained by using trusted, real-time security software like 360 Total Security on your Windows or macOS desktop — your most reliable partner in keeping these threats from ever taking hold.
Frequently Asked Questions
Q1: Can a website actually scan my computer and detect viruses?
No. This is one of the most important facts to internalize. Websites running in a web browser operate in a strictly sandboxed environment and have no technical capability to access, read, or scan the files on your hard drive. Any website claiming to have detected viruses on your computer is categorically lying. Only software that is properly installed on your operating system — like a legitimate antivirus program — can perform actual system scans.
Q2: I accidentally clicked a button in a fake warning. What should I do immediately?
Do not panic — act quickly and methodically. First, disconnect your computer from the internet (unplug your ethernet cable or disable Wi-Fi) to prevent any malware from communicating with external servers. Then use Task Manager to close your browser entirely. Next, reconnect to the internet, open your legitimate antivirus software (or download 360 Total Security from its official site), and run a comprehensive full system scan immediately. Follow the remediation steps for any threats found. If you entered payment information, contact your bank or card provider immediately to report potential fraud and request a card freeze.
Q3: How do I tell if a security notification is from my real 360 Total Security software versus a fake?
Genuine 360 Total Security notifications will always appear as Windows system notifications (in the bottom-right corner of your screen) or within the 360 Total Security application interface itself — never inside a web browser window. They will identify specific threat names and file paths, offer clear remediation options without demanding payment, and will never ask for your credit card information to remove a threat. If in doubt, close the notification and open 360 Total Security directly from your Start Menu to check its dashboard for any real alerts.
Q4: Are fake virus warnings only a Windows problem, or do Mac users face them too?
Both Windows and macOS users encounter fake virus warnings, though Windows users are targeted more frequently due to the platform’s larger market share. Mac users commonly encounter browser-based fake alerts claiming their “Mac is infected” or that their “Apple Security” has detected threats. The identification and response strategies in this guide apply equally to both platforms. 360 Total Security offers desktop protection for both Windows and macOS users.
Q5: Should I report fake virus warnings, and if so, to whom?
Yes, reporting these scams is valuable — it helps authorities track and shut down criminal operations and protects other users. In the United States, report scams to the Federal Trade Commission (FTC) at reportfraud.ftc.gov. In the United Kingdom, use Action Fraud at actionfraud.police.uk. In the European Union, contact your national cybercrime reporting center. You can also report malicious websites directly to Google Safe Browsing (safebrowsing.google.com/safebrowsing/report_phish/) and to your browser vendor. Every report contributes to a safer internet ecosystem.
About the Author: This article was written by a Senior Technical Writer and Cybersecurity Content Specialist with over a decade of experience translating complex threat intelligence and security research into actionable guidance for everyday PC users and IT professionals. With a background spanning endpoint security, digital forensics, and user education, the author collaborates with cybersecurity researchers and antivirus engineers to ensure all published content reflects current, accurate, and practically applicable security best practices. Their work has been referenced by cybersecurity awareness programs and enterprise IT training curricula across multiple regions.
Learn more about 360 Total Security