Recently, 360 Security Center discovered a type of actively spreading CryptoMiner Trojan infected 140 thousands computers in two days. The Trojan creates a copy of PowerShell component in the system as “%SYSTEMDRIVE%\Program Files\Windows NT\Accessories\task.exe” and hides itself in scheduled tasks to avoid the detection of antivirus software. We named the Trojan “HiddenPowerShellMiner”.
Analysis
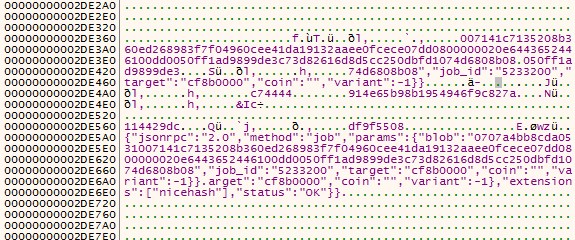
The Trojan is bundled with various game cracks. While victims run the installer of the games, the Trojan downloads a script from URL hxxp://80.82.79.12/update.php and launch it. The script duplicates powershell.exe as “%SYSTEMDRIVE%\Program Files\Windows NT\Accessories\task.exe” to avoid antivirus detection. After duplicating Powershell, the scheduled tasks will be created with parameters for downloading the cryptominer. The common scheduled tasks created are as follows: Tasks\Microsoft\Windows\SyncCenter\SyncCenter Tasks\Microsoft\Windows\MobilePC\MobilePC Tasks\Microsoft\Windows\Maintenance\Maintenance Tasks\Microsoft\Windows\Location\Location The complete parameter is shown below:
The parameters need to be decrypted for downloading the cryptominer application.
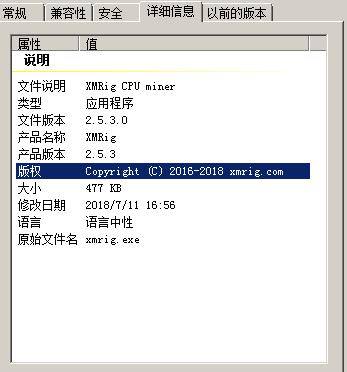
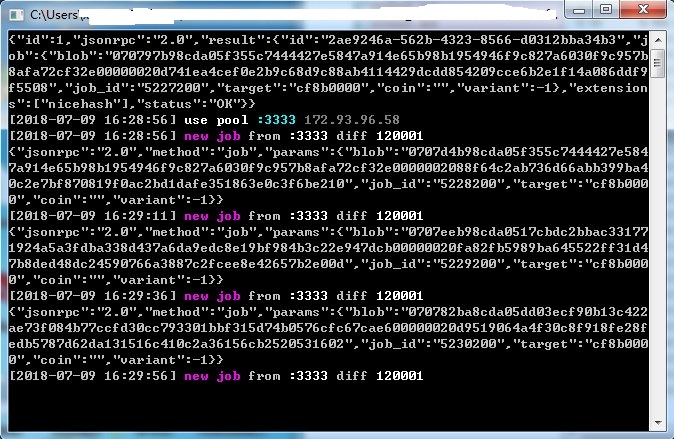
One application is a Monroe miner “c:\programdata\windows\dlhosts.exe”. It is actually a modified open source code “Xmrig”.
The other application “c:\programdata\windows\dlchosts.exe” is a Ethereum miner which is modified from an open source GitHub project “ethminer”. It downloads a graphics card module, http://80.82.79.12/ups3/nvml.dll, of NVIDIA, identifies victims’ graphics card configuration and mines Ethereum by graphics card.
Reminder
Recently, we have found that a lot of CryptoMiner Trojans are actively spreading in the wild. We strongly recommend users to enable antivirus software while installing new applications. Users are also recommended to run virus scan with 360 Total Security to avoid falling victim to CryptoMiner.
Learn more about 360 Total Security