The PUBG ransomware which was popular in this April forced players to play the game blew up on some forums such as Reddit and Steam Community. The difference between PUBG ransomware and other ransomware is that it only forces PUBG players to play the game for one hour rather than asking users to pay ransom. Hence, it is considered as a joke rather than an annoying issue. However, just like what 360 Security Center concerns: This kind of game malware has begun to be further intensified.
The updated PUBG ransomware is forcing players to play the game for 3596400 seconds, which is 999 HOURS, instead of one hour.
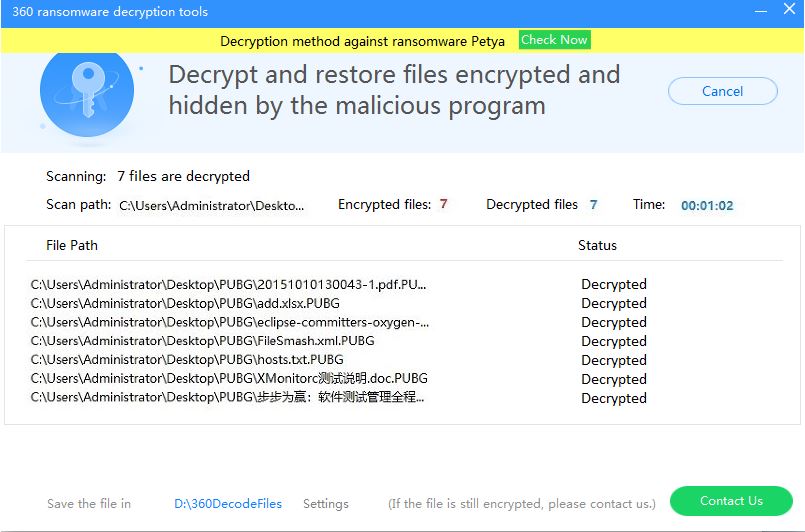
360 Security Center is the first to detect and decrypt the updated version of the malware. Like the previous version, it would encrypt all files of users, including pictures, music, video and documents. The difference between the two versions is that the updated malware would not decrypt the user’s files when detecting the process of TslGame.exe. The user’s files would be decrypted until the process has run for 3596400 seconds.
Since it is nearly impossible for players to play the game for 999 HOURS, we are going to provide a good solution for those unlucky players:
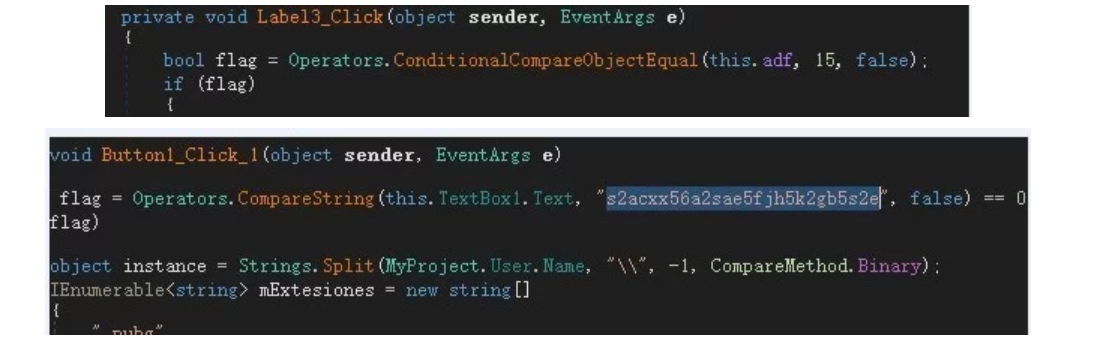
Enter the string “s2acxx56a2sae5fjh5k2gb5s2e” into the password box and press the decrypt button 15 times to easily decrypt the files.
Use the string to decrypt files:
Tips
The latest PUBG ransomware does not cause huge damage to players, and we already provided the solution, but what we worry about is its request to users will be a lot intensified in the future. Thus, we would like to alert our users that do not underestimate this kind of ransomware and increase the alertness.
Also, we recommend our users to install 360 Total Security to gear a Ransomware Shield to prevent attacks in the first place. What to do if the computer is hijacked by ransomware? Our Ransomware Decryption Tool can help users bring back files from more than 80 ransomware.
Learn more about 360 Total Security