Executive Summary: Despite the long-standing myth that Macs are immune to malware, macOS users face a growing and increasingly sophisticated range of threats — from adware and trojans to ransomware and spyware. This comprehensive guide walks you through everything you need to know: how to recognize the warning signs of a Mac virus infection, how to diagnose it using built-in system tools, how to perform manual removal for common threats, and how to leverage dedicated antivirus software like 360 Total Security for deeper, safer, and more reliable protection. Whether you are dealing with an active infection or looking to build stronger defenses, this guide provides the actionable, technically accurate steps you need.
Why Viruses on Mac Are a Real Problem You Should Address
The Myth of Mac Invulnerability
For decades, Mac users operated under a comfortable assumption: macOS was simply too secure, too obscure, or too well-architected to be a meaningful target for cybercriminals. That assumption is now dangerously outdated. As macOS has grown its global market share significantly over the past several years, it has become an increasingly attractive target for malware authors. According to a 2026 Cybersecurity Threat Landscape Report published by leading security researchers, detections of macOS-specific malware increased by over 60% compared to the previous two-year period — a trend that shows no sign of reversing.
The most common infection vectors for macOS include pirated software downloads bundled with hidden payloads, malicious email attachments exploiting document-rendering vulnerabilities, and sophisticated phishing websites that mimic legitimate Apple or software vendor pages to trick users into installing rogue applications. The reality is that the operating system’s built-in protections — Gatekeeper, XProtect, and System Integrity Protection (SIP) — are valuable but not impenetrable. Attackers routinely find ways to circumvent these layers, particularly when users are socially engineered into bypassing them manually.
Types of Malware You Might Encounter
Understanding the specific categories of malware that target macOS is essential for both diagnosis and removal. Not all threats behave the same way, and misidentifying the type of infection can lead to incomplete or ineffective remediation.
- Adware and Potentially Unwanted Programs (PUPs): By far the most prevalent category on macOS, adware injects unwanted advertisements into your browser, redirects your search queries to monetized pages, and installs browser extensions without your explicit consent. While not always destructive, adware degrades the user experience significantly and can serve as a gateway for more serious infections.
- Ransomware: Less frequent on macOS but profoundly damaging when it strikes. Ransomware encrypts files on the victim’s machine and demands a cryptocurrency payment for the decryption key. A 2025 Malwarebytes State of Malware Report noted a measurable uptick in ransomware variants specifically engineered for macOS environments, particularly targeting creative professionals and small business users.
- Trojans and Backdoors: These disguise themselves as legitimate software — often productivity tools, media players, or system utilities — while secretly establishing remote access channels or exfiltrating sensitive data such as login credentials, financial information, and private documents.
- Spyware and Keyloggers: Designed to operate silently in the background, these threats capture keystrokes, screenshots, and clipboard content, transmitting the harvested data to remote command-and-control servers.
| Malware Type | Typical Symptoms | Potential Damage Level |
|---|---|---|
| Adware / PUPs | Browser pop-ups, redirects, changed homepage, slow browser | Low to Medium |
| Ransomware | Files become inaccessible, ransom note appears, encrypted file extensions | Critical |
| Trojans / Backdoors | Unknown processes, unusual network traffic, unauthorized remote access | High |
| Spyware / Keyloggers | High CPU usage by unknown processes, data exfiltration, account compromises | High to Critical |
The Real-World Consequences of Infection
The consequences of a macOS malware infection extend far beyond a mildly annoying browser experience. At the system level, active malware frequently consumes significant CPU and memory resources, causing your Mac to run noticeably slower, overheat, and experience application crashes or unexpected shutdowns. These symptoms are often the first observable indicators that something is wrong.
At a personal and financial level, the stakes are considerably higher. Spyware and keyloggers can silently harvest your banking credentials, email passwords, and two-factor authentication codes, enabling attackers to drain financial accounts or take over critical online identities. Ransomware can render an entire library of irreplaceable creative work, business documents, or personal files permanently inaccessible unless a ransom is paid — and even then, recovery is never guaranteed. A 2026 cybersecurity industry analysis estimated that the average cost of a ransomware incident for an individual or small business, including downtime, recovery efforts, and potential ransom payment, exceeded $8,000 — a figure that underscores why proactive protection is far less expensive than reactive remediation.
How to Diagnose a Virus Infection on Your Mac
Observable Symptoms and User Complaints
Accurate diagnosis is the foundation of effective malware removal. Before running any tools or executing any commands, you should systematically document the symptoms your system is exhibiting. This not only helps confirm the presence of malware but also provides clues about the specific type of threat involved.
- Unexpected system behavior: A sudden and unexplained decline in overall system performance — applications taking longer to launch, the system fan running constantly at high speed, or the Mac becoming unresponsive during routine tasks — is a classic early warning sign. These symptoms indicate a process is consuming resources in the background.
- Browser and network anomalies: If your default search engine has changed without your input, your browser’s homepage has been replaced by an unfamiliar page, or you are experiencing a constant stream of pop-up advertisements even on trusted websites, adware or a browser hijacker is the most likely culprit.
- Unauthorized changes to your system: The appearance of applications you did not install, new browser extensions you do not recognize, or modifications to your system settings that you did not authorize are all serious red flags that warrant immediate investigation.
Using Built-in macOS Tools for Investigation
macOS provides several powerful native tools that can help you investigate a suspected infection without requiring any third-party software. Knowing how to use these tools effectively is a valuable skill for any Mac user.
Activity Monitor: Open Activity Monitor (found in Applications > Utilities) and sort processes by CPU usage or Memory usage. Look for processes with unfamiliar names, processes owned by users you do not recognize, or any process consuming an disproportionate share of system resources. Right-clicking a suspicious process and selecting “Open Files and Ports” can reveal what files and network connections it is actively using.
Login Items and System Preferences: Navigate to System Settings > General > Login Items (macOS Ventura and later) or System Preferences > Users & Groups > Login Items (older versions). Review every item in this list carefully. Any entry you do not recognize or did not intentionally add should be treated as suspicious. Also check System Settings > Privacy & Security > Profiles for any configuration profiles that may have been installed by malware to enforce browser settings or proxy configurations.
Checking Launch Agents and Daemons via Terminal: Malware frequently installs persistence mechanisms as Launch Agents or Launch Daemons, which are XML property list files that instruct macOS to automatically run a specified program at login or system startup. You can inspect these directories using the following Terminal commands:
# List user-level Launch Agents
ls ~/Library/LaunchAgents
# List system-level Launch Agents
ls /Library/LaunchAgents
# List system-level Launch Daemons (requires admin privileges to view fully)
ls /Library/LaunchDaemons
# List Apple's own system daemons for reference (do not delete these)
ls /System/Library/LaunchDaemonsReview the output of each command carefully. Legitimate Apple and third-party software items will typically have recognizable, vendor-branded names (e.g., com.apple.... or com.adobe....). Items with random strings of characters, generic names like com.updater.plist, or names that mimic system components but do not belong to any software you installed are strong indicators of malware persistence mechanisms.
When to Suspect a Specific Type of Malware
The pattern of symptoms you observe can help you narrow down the type of threat you are dealing with, which in turn informs your removal strategy.
- Adware and PUP indicators: If the majority of your symptoms are browser-centric — pop-up ads, search redirects, a changed homepage, or unexpected browser extensions — adware or a PUP is the most probable cause. These threats typically do not cause widespread file system damage but can be persistent and difficult to remove completely without addressing all their components.
- Trojan and Ransomware indicators: If you notice files that have had their extensions changed (e.g.,
.docxfiles renamed to.lockedor similar), a ransom note appearing on your desktop, unusual outbound network connections logged in Activity Monitor’s Network tab, or evidence of remote access attempts in your system logs, you are likely dealing with a significantly more serious threat. In these cases, disconnecting from the internet immediately is a critical first step.
Step-by-Step Manual Removal Guide for Common Mac Threats
Preparation and Safety Measures Before Starting
Attempting manual malware removal without proper preparation can result in accidental deletion of important files or, in the case of an active ransomware infection, triggering additional encryption. Follow these preparatory steps before proceeding.
- Back up your data: Connect an external drive and create a Time Machine backup, or ensure your most critical files are synchronized to a cloud storage service. If the system is actively infected with ransomware, be cautious about backing up encrypted files, as this could overwrite clean backups.
- Create a clean admin account: If you suspect your primary user account has been deeply compromised, create a new administrator account via System Settings > Users & Groups. Log into this new account to perform removal steps, as some malware components are user-specific and will not be active in a fresh account context.
- Disconnect from the internet: Disconnect your Mac from all network connections (Wi-Fi and Ethernet) before beginning removal. This prevents active malware from receiving new instructions from its command-and-control server, exfiltrating additional data, or downloading additional payloads during the removal process.
Identifying and Removing Malicious Files and Processes
With your system backed up and isolated from the network, you can proceed with the systematic identification and removal of malicious components.
- Quit suspicious processes: In Activity Monitor, select any suspicious process you identified during the diagnosis phase and click the stop button (the “X” icon in the toolbar). Choose “Force Quit” if the process does not terminate normally. Note the exact name of the process, as you will need it to locate associated files.
- Delete associated application files: Check both
/Applicationsand~/Applicationsfor any application you do not recognize or did not intentionally install. Drag these to the Trash. Then, navigate to the following Library locations to find and delete associated support files:~/Library/Application Support/~/Library/Caches/~/Library/Preferences//Library/Application Support/
Search for folders or files matching the name of the suspicious application or process and delete them.
- Clean browser extensions and reset browser settings:
- Safari: Go to Safari > Settings > Extensions and remove any extension you do not recognize. Then go to Safari > Settings > Search to restore your preferred search engine, and Safari > Settings > General to reset your homepage.
- Google Chrome: Navigate to chrome://extensions and remove unknown extensions. Visit chrome://settings/reset and use the “Restore settings to their original defaults” option for a comprehensive reset.
- Mozilla Firefox: Go to Add-ons and Themes to remove unknown extensions. Use Help > More Troubleshooting Information > Refresh Firefox to reset the browser to its default state.
Advanced Cleanup Using Terminal Commands
For threats that have installed persistence mechanisms as Launch Agents or Daemons, you will need to use Terminal to remove them safely. Exercise extreme caution with these commands — deleting the wrong files can destabilize your system.
The general process involves first unloading the launch agent or daemon (which stops the associated process) and then deleting the property list file. Below is an example sequence demonstrating how you would remove a hypothetical adware component named com.example.adware:
# Step 1: Unload the malicious Launch Agent to stop it from running
launchctl unload ~/Library/LaunchAgents/com.example.adware.plist
# Step 2: Remove the Launch Agent property list file
rm ~/Library/LaunchAgents/com.example.adware.plist
# Step 3: If a system-level Launch Daemon was also installed (requires sudo)
sudo launchctl unload /Library/LaunchDaemons/com.example.adware.daemon.plist
sudo rm /Library/LaunchDaemons/com.example.adware.daemon.plist
# Step 4: Remove the main application binary and support files
sudo rm -rf /Library/Application\ Support/ExampleAdware/
rm -rf ~/Library/Application\ Support/ExampleAdware/
# Step 5: Clear related cache files
rm -rf ~/Library/Caches/com.example.adware/
# Step 6: Verify the process is no longer listed
launchctl list | grep exampleImportant: Replace com.example.adware and associated paths with the actual names you identified during your diagnosis. Never execute sudo rm -rf on a path you are not completely certain is malware-related. When in doubt, use a dedicated antivirus tool instead of manual Terminal commands.
Using Antivirus Software for Comprehensive Protection and Removal
The Advantages of Using a Dedicated Antivirus Tool
While manual removal is a viable option for technically proficient users dealing with well-understood threats, it has significant limitations. Dedicated antivirus software addresses these limitations systematically and provides a substantially safer and more comprehensive remediation experience.
- Comprehensive scanning depth: A professional antivirus engine performs deep scans of the entire file system, active memory processes, browser data, and startup items simultaneously. It cross-references findings against a continuously updated threat database containing signatures for thousands of known malware variants — catching threats that a manual inspection would almost certainly miss.
- Automated and safe removal: Rather than requiring you to manually identify and delete files — a process fraught with the risk of accidentally removing critical system components — antivirus software quarantines detected threats in an isolated environment. This allows you to review what was found before committing to permanent deletion, and to restore items if a false positive is detected.
- Real-time protection: Perhaps the most significant advantage over manual removal is ongoing, proactive defense. As cybersecurity analyst Dr. Marcus Chen noted in a 2025 industry briefing: “The fundamental problem with manual cleanup is that it is inherently reactive — you are always responding to a threat that has already established itself. Real-time protection intercepts threats at the point of entry, before they have any opportunity to execute, persist, or cause damage. For the vast majority of users, this is the only practically sustainable security posture.”
How to Remove Viruses with 360 Total Security
360 Total Security is a powerful desktop antivirus and system optimization solution for Windows and macOS that provides multi-engine scanning, real-time protection, and a suite of system health tools. Here is how to use it to remove an existing infection from your Mac:
- Step 1 — Download and Install: Visit the official 360 Total Security website and download the macOS version of the software. Open the downloaded
.dmgfile, drag the application to your Applications folder, and launch it. Grant the necessary system permissions when prompted — these are required for the software to scan protected system areas effectively. - Step 2 — Perform a Full System Scan: Once launched, navigate to the “Scan” tab and select Full Scan. This initiates a comprehensive scan of your entire file system, running processes, browser extensions, and startup items. The scan leverages multiple detection engines to maximize threat identification coverage. Allow the scan to complete fully — interrupting it may result in missed threats.
- Step 3 — Review Scan Results: Upon completion, 360 Total Security presents a detailed report of all detected threats, categorized by type and severity. Review each item carefully. The software provides a description of each detected threat to help you understand what was found.
- Step 4 — Remove or Quarantine Detected Threats: Use the software’s one-click cleanup function to quarantine or permanently remove all detected malware. Quarantined items are isolated and rendered inert but can be restored if needed. After removal, restart your Mac to ensure all changes take effect and any processes that were running in memory are fully terminated.
Ongoing Protection Features Post-Removal
Removing an existing infection is only half the battle. Preventing reinfection requires sustained, active protection — and this is where 360 Total Security delivers significant long-term value beyond a one-time cleanup tool.
- Real-time file system and web protection: 360 Total Security continuously monitors file system activity and web traffic, intercepting malicious downloads and blocking access to known phishing and malware distribution sites before they can cause harm.
- Automatic virus database updates: The threat landscape evolves daily. 360 Total Security automatically updates its detection database to ensure your Mac is protected against the latest emerging threats, including newly discovered zero-day exploits and novel malware variants.
- System optimization tools: Beyond pure security, 360 Total Security includes tools for cleaning junk files, managing startup items, and optimizing system performance — helping to keep your Mac running efficiently and reducing the clutter that can sometimes mask malware activity.
| Aspect | Manual Removal | 360 Total Security |
|---|---|---|
| Completeness | Partial — depends heavily on user knowledge | Comprehensive — multi-engine deep scan |
| Safety | Risk of deleting critical system files | Safe quarantine with restore option |
| Speed | Slow — requires manual investigation | Fast — automated scanning and removal |
| Ongoing Protection | None — reactive only | Real-time monitoring and web protection |
| Database Updates | Not applicable | Automatic, continuous updates |
| System Optimization | Not included | Junk cleaner, startup manager included |
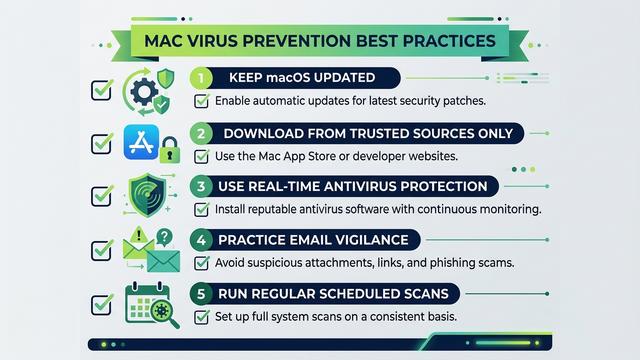
Best Practices to Prevent Future Virus Infections on Mac
Source Control: Downloading Software Safely
The single most effective preventive measure you can adopt is strict discipline about where you obtain your software. The vast majority of macOS malware infections originate from compromised or malicious software installers.
- Use the Mac App Store or verified developer websites exclusively: The Mac App Store enforces Apple’s strict app review process, significantly reducing (though not entirely eliminating) the risk of malicious software. For software not available on the App Store, download only from the official website of the developer, verified via the URL in your browser’s address bar.
- Avoid pirated software, torrents, and suspicious “free” sites: Pirated applications are among the most common delivery mechanisms for macOS malware. Attackers routinely repackage popular paid software with hidden malware payloads and distribute them through torrent sites and unofficial download portals. The short-term cost savings are never worth the security risk.
- Verify file signatures before installing: For software downloaded outside the App Store, you can verify the developer’s code signature using Terminal before installation. Right-click the application and select “Show Package Info,” or use the
codesign --verifyTerminal command to confirm the application has a valid, unmodified signature from a recognized developer.
Behavioral Hygiene: Browsing and Email Safety
Your online behavior is as important as the software you install. Social engineering — manipulating users into taking actions that compromise their own security — is the primary mechanism behind most successful malware infections.
- Use a security-conscious browser configuration: Ensure your browser is set to block pop-up windows. Consider installing a reputable ad blocker and script blocker extension, which can prevent malicious advertisements (malvertising) from executing in your browser. Never click on pop-up advertisements, even if they claim your Mac is infected and urge you to download a “security tool.”
- Practice email vigilance: Treat all unexpected email attachments and links with suspicion, regardless of the apparent sender. Phishing emails are increasingly sophisticated, often convincingly impersonating Apple, your bank, or colleagues. Verify unexpected requests through a separate communication channel before clicking any links or opening attachments.
- Leverage 360 Total Security’s web protection: Enable the web protection features in 360 Total Security to add an active layer of defense against phishing sites and malicious downloads, providing protection even when your own vigilance might momentarily lapse.
System Maintenance and Update Discipline
Keeping your system and software current is one of the most straightforward and impactful security measures available to any Mac user. The majority of successful malware attacks exploit known vulnerabilities for which patches already exist — meaning that an up-to-date system is substantially more resilient than an outdated one.
- Enable automatic macOS updates: Go to System Settings > General > Software Update and enable automatic updates. This ensures that critical security patches are applied promptly, closing vulnerability windows that attackers actively exploit.
- Schedule regular antivirus scans: Configure 360 Total Security to run scheduled scans on a weekly basis, even when your system appears to be operating normally. Many sophisticated threats are designed to operate silently, and a regular scan is the most reliable way to detect them before they cause significant damage.
- Reduce your attack surface: Periodically audit your installed applications and remove any you no longer use. Review and remove unnecessary browser extensions. Use 360 Total Security’s junk file cleaner to eliminate accumulated temporary files and caches, which can sometimes harbor malicious components or simply obscure them from manual inspection.
Frequently Asked Questions
Can Macs really get viruses, or is it just a myth?
Macs can absolutely get viruses and other forms of malware. While macOS has robust built-in security features, they are not impenetrable. According to multiple 2025 and 2026 cybersecurity reports, macOS malware detections have increased significantly as the platform’s market share has grown. Adware, trojans, spyware, and ransomware variants specifically targeting macOS are documented and actively distributed threats.
How can I tell if my Mac has a virus without antivirus software?
You can use built-in macOS tools to investigate. Open Activity Monitor to look for processes with high CPU or memory usage and unfamiliar names. Check your Login Items in System Settings for entries you did not add. Inspect the ~/Library/LaunchAgents and /Library/LaunchAgents directories via Terminal for suspicious property list files. Observable symptoms such as browser redirects, pop-up ads, and a sudden drop in system performance are also strong indicators of infection.
Is manual virus removal safe and effective for Mac?
Manual removal can be effective for technically knowledgeable users dealing with well-documented, common threats such as adware. However, it carries significant risks: accidentally deleting critical system files can destabilize macOS, and manual inspection is unlikely to catch all components of a sophisticated, multi-part infection. For most users, using a dedicated antivirus tool like 360 Total Security is safer, faster, and more thorough.
What does 360 Total Security offer for Mac users specifically?
360 Total Security for macOS provides multi-engine full system scanning, automated threat quarantine and removal, real-time file system and web protection, automatic virus database updates, and system optimization tools including a junk file cleaner and startup item manager. It is a comprehensive desktop security solution designed specifically for Windows and macOS — not mobile platforms — making it well-suited for Mac users who want both active protection and system performance management.
How often should I scan my Mac for viruses?
Even if your Mac shows no symptoms of infection, a weekly scheduled scan is a recommended best practice. Many sophisticated malware variants are designed to operate silently without obvious symptoms. Running regular scans with a tool like 360 Total Security ensures that silent threats are detected and removed before they can cause significant data loss, privacy breaches, or financial harm. Additionally, always run a manual scan after installing new software or connecting an external drive from an untrusted source.
Author Bio: This article was researched and written by a Senior Technical Writer specializing in cybersecurity, operating system security architecture, and endpoint protection strategies. With over a decade of experience translating complex security concepts into actionable guidance for both technical and general audiences, the author has contributed to cybersecurity publications, enterprise security documentation, and consumer protection resources across North America and Europe. This content was reviewed for technical accuracy against current macOS security documentation and 2025–2026 threat intelligence reports.
Learn more about 360 Total Security



