Google has announced that it will start marking HTTP connections as “non-secure” on its browser Chrome.
From Chrome 56 (expected to be released in January 2017), Google will start marking HTTP sites as “non-secure” in an effort to highlight users the risk of sending sensitive information on HTTP sites, as well to encourage webmasters to adopt the more secure HTTPS protocol on their websites.
Current and previous versions of Chrome do not highlight HTTP traffic with any special indicator (as they do with HTTPS traffic). According to the company, “users do not perceive the lack of a ‘secure’ icon as a warning”. Regular HTTP protocol sends information unencrypted, being this a dangerous practice, especially when transmitting passwords and credit card numbers, that an attacker can easily intercept.
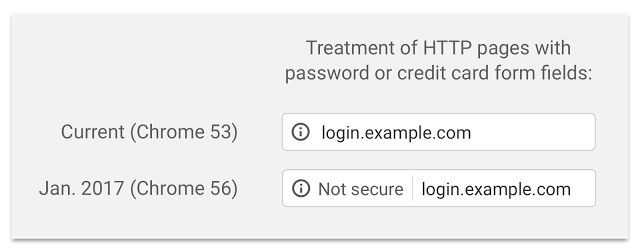
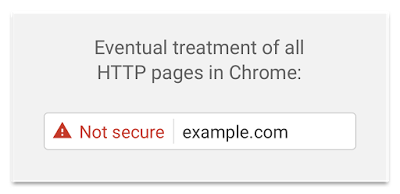
Google states on its blog that it will start deploying the HTTP indicator in a progressive way. Starting with Chrome 56, the browser will first label as not secure HTTP pages with credit card or password form fields, since these are specially sensitive types of information. In further releases, Google plans to mark all HTTP pages as not secure, first in the browser’s Incognito Mode, since its users might have higher sensitivity towards privacy, and finally to all Chrome HTTP traffic. Google plans to mark in a final stage all HTTP connections with the red triangle currently used for broken HTTPS.
The company recommends webmasters to start moving to HTTPS, arguing that this feature is cheaper and easier than ever before, and it enables powerful new features, such as user media sharing, that are too sensitive for HTTP connections.
HTTPS protocol transfers HTTP traffic encrypted by Transport Layer Security or Secure Sockets Layer. Besides adding bidirectional encryption of communication, HTTPS also provides authentication of the website and the associated web server, protecting against impersonation, eavesdropping and other man-in-the-middle attacks. In other words, users can have a guarantee that no one is able to intercept their information, unlike unencrypted HTTP communications.
Learn more about 360 Total Security



