[Tips: Install 360 Total Security to prevent CryptoMiner attacks]
Recently, 360 Security Center discovered an actively spreading CryptoMiner Trojan. The Trojan abused the vulnerability, CVE-2018-4878, of Adobe Flash Player and was distributed via website with built-in script. The vulnerability was exposed in February this year and already fixed. We named it “WagonlitSwfMiner”.
Analysis
The Trojan built by NSIS (Nullsoft Scriptable Install System) is downloaded while user visits the malicious website which contains swf file with the vulnerability. It creates electrotonus.dll and Wagonlit.bin after launched. The dll file is filled with a huge amount of trash commands and dynamic API to avoid static analysis. electrotonus.dll decrypts the core script of the Trojan by loading Wagonlit.bin. The core script will be written into svchost process remotely for mining Cryptocurrency XMR. The Trojan will then copy itself to %appdata%/blowoff.exe and add itself as a startup item. blowoff.exe releases electrotonus.dll which will call FindBit32 to export the main function for running mining script.
electrotonus.dll module loads Wagonlit.bin
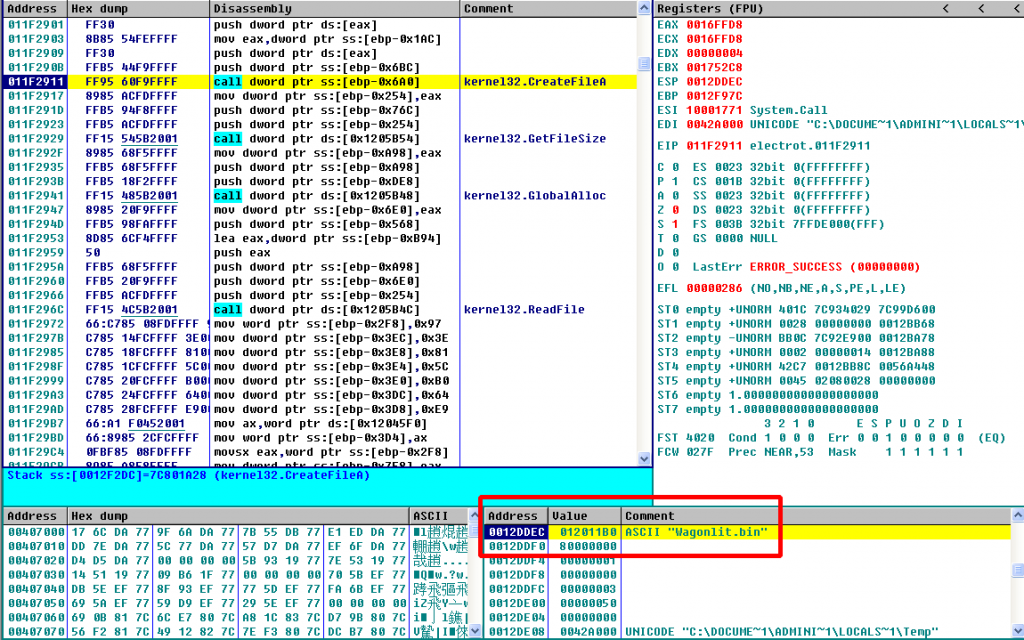
Decrypt the Shellcode content from the file header of Wagonlit.bin recurrently.
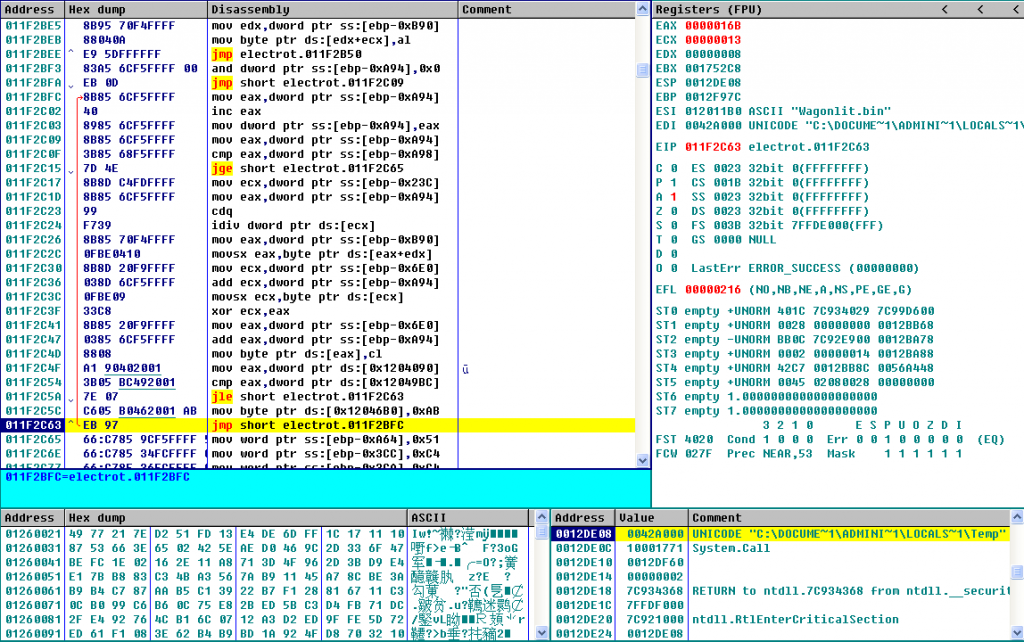
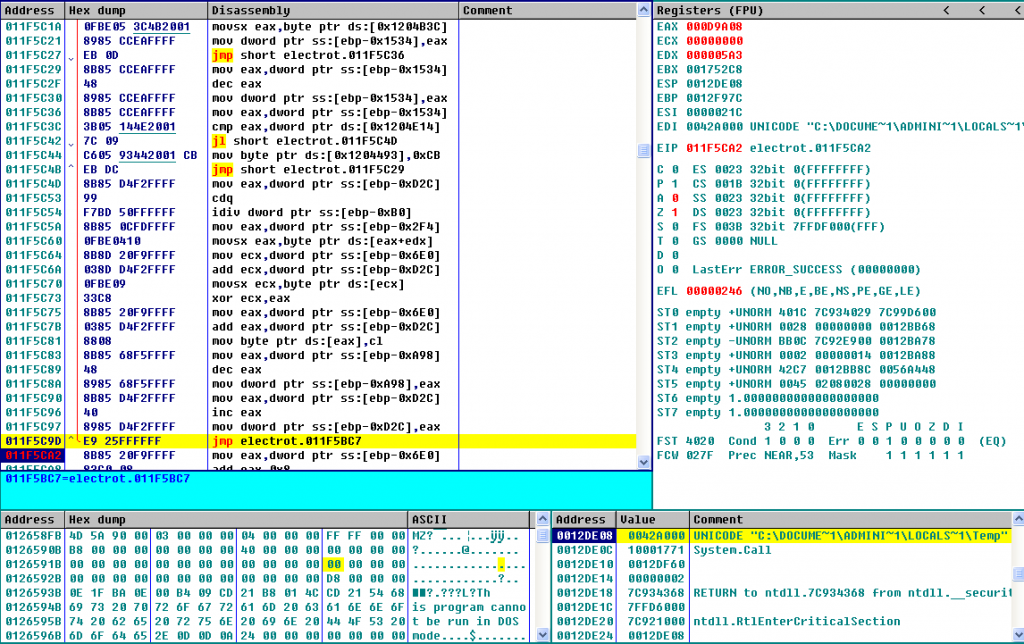
Decrypt the core PE file from Wagonlit.bin recurrently.
Launch msiexec.exe for adding itself into startup items remotely to avoid antivirus detection.
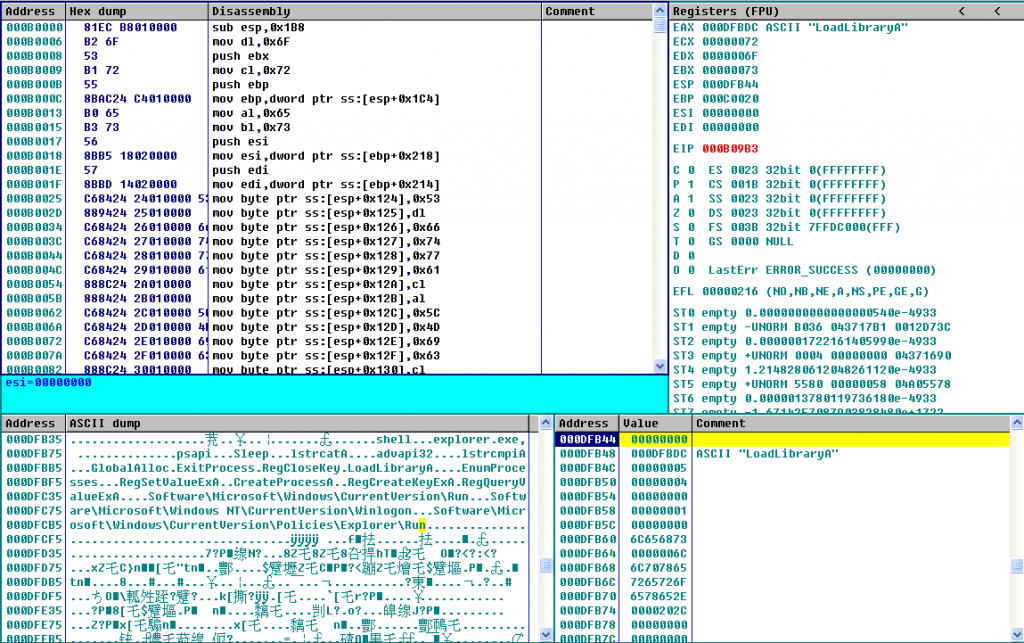
Launch blowoff.exe, write the core PE file into the decrypted Shellcode and run the Trojan script.
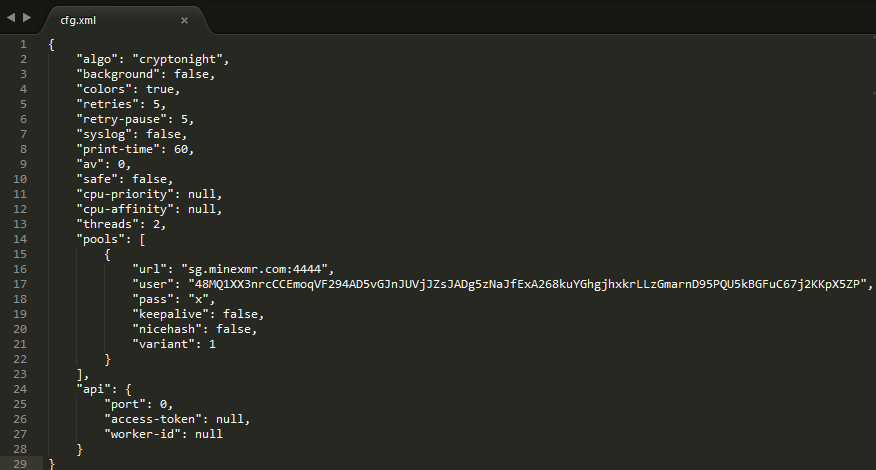
The Trojan script will send a requset to http://nhocboconfig.ru/bo/config.txt for acquiring latest configuration.It will decrypt online configuration if the request responses successfully. Currently the URL is invalid, the local configuration will be decrypted instead. The decrypted content shown below will be written into %appdata%/ KcEqSDTxqP / cfg.
“url”: “sg.minexmr.com:4444”,
“user”: “48MQ1XX3nrcCCEmoqVF294AD5vGJnJUVjJZsJADg5zNaJfExA268kuYGhgjhxkrLLzGmarnD95PQU5kBGFuC67j2KKpX5ZP”,
“pass”: “x”,
svchost.exe will be launched and injects the open source miner script of XMR into the Trojan script to start mining. The parameters are shown below.
“C:\WINDOWS\System32\svchost.exe” -c “C:\Documents and Settings\All Users\Application Data\KcEqSDTxqP\cfg”
The Trojan script will verify the parameters itself. If the parameter contains –show-window, the miner will display a command line interface and show the mining process.
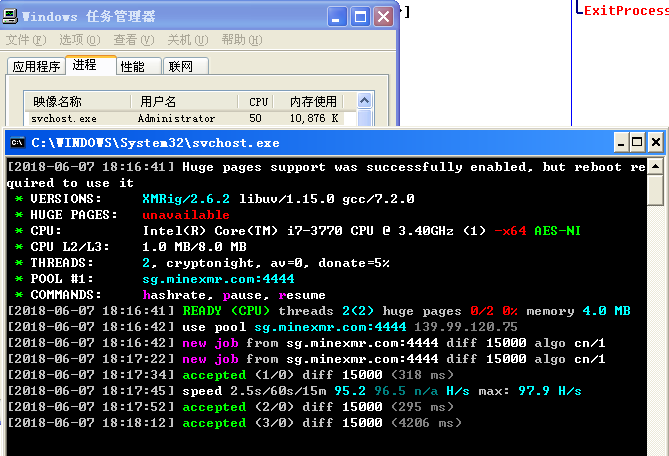
The Trojan script also watches if the svchost mining process is exist, or will restart it to keep it alive.
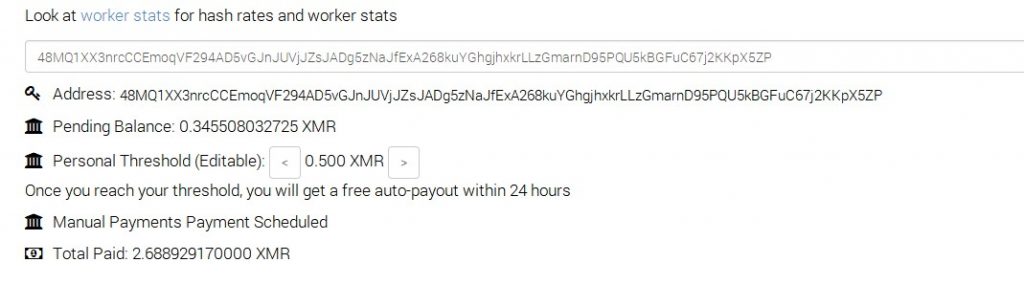
The income in these two days:
Reminder
Recently, we have found that a lot of CryptoMiner Trojans are actively spreading in the wild. We strongly recommend users to enable antivirus software while installing new applications. Users are also recommended to run virus scan with 360 Total Security to avoid falling victim to CryptoMiner.
Download 360 Total Security: https://www.360totalsecurity.com
Learn more about 360 Total Security