Executive Summary: The ‘Operation did not complete’ virus error in Windows 10 is one of the most alarming security warnings a user can encounter. It signals that your antivirus software — whether Windows Defender or a third-party solution — has detected a threat but failed to neutralize it. This comprehensive guide walks you through every layer of the problem: understanding what triggers the error, executing a systematic manual removal process, leveraging advanced tools like 360 Total Security for deep-level remediation, applying emergency recovery techniques for the most stubborn infections, and finally building a proactive defense strategy to ensure this error never disrupts your system again. Whether you are a casual user or an IT professional, this guide provides the precise, actionable steps needed to reclaim full control of your Windows 10 PC.
What Does ‘Operation Did Not Complete’ Virus Error Mean in Windows 10?
When Windows 10 displays the message ‘Operation did not complete successfully because the file contains a virus or potentially unwanted software’, it is not a routine notification — it is a critical security alert demanding immediate attention. Understanding the root cause of this error is the essential first step before any remediation can begin.
Decoding the Error: Is It a Virus or a System Glitch?
The error originates most commonly from Windows Defender or a third-party antivirus engine that has successfully identified a threat but cannot complete the quarantine or deletion process. This failure can stem from two distinct scenarios, and distinguishing between them determines your entire response strategy.
Scenario 1: A Persistent Malware Infection. The most serious cause. The malware has embedded itself deeply enough into the operating system — injecting into running processes, locking its own files, or granting itself system-level privileges — that the security software cannot obtain the necessary file access to delete it. According to Microsoft’s official documentation on Windows Defender error codes, error states in the 0x80070 family frequently indicate that a file is locked by an active process, a classic hallmark of a live, running infection.
Scenario 2: Corrupted System Files Triggering False Positives. In some cases, legitimate Windows system files become corrupted and are misidentified by heuristic scanning engines as malicious. A 2025 Microsoft Security Intelligence Report noted that a measurable percentage of user-reported removal failures were attributable to corrupted OS components rather than active malware. This distinction is critical: attempting aggressive manual deletion in this scenario could damage your operating system further.
The most common malware families associated with this specific error include:
- Trojans (e.g., Trojan:Win32/Wacatac) that inject into legitimate system processes like
svchost.exe. - Ransomware downloaders that establish persistence before deploying their payload, making early removal critical.
- Adware and PUPs (Potentially Unwanted Programs) that use rootkit-like techniques to protect their core executable files from deletion.

Immediate Risks: What Happens If You Ignore This Warning?
Dismissing this error and continuing normal computer use is one of the most dangerous decisions a Windows 10 user can make. The consequences escalate rapidly across three dimensions:
1. System Performance Degradation. Active malware consumes significant CPU and RAM resources. Users typically report unexplained CPU spikes to 90–100%, dramatically slower boot times, and frequent application crashes. These are not mere inconveniences — they are symptoms of a system under active attack.
2. Data Security Threats. Depending on the malware variant, the risks to your personal data are severe. Trojans can silently exfiltrate passwords, banking credentials, and personal documents to remote command-and-control servers. Ransomware downloaders, if allowed to execute their payload, can encrypt every file on your drive and connected network shares, demanding payment for decryption. A 2026 Cybersecurity Ventures report projected that ransomware attacks would cost businesses and individuals a combined $275 billion annually, with a significant portion originating from exactly these kinds of unresolved initial warnings. Furthermore, your machine can be conscripted into a botnet, using your bandwidth and IP address for criminal activities without your knowledge.
3. Network Vulnerability. An infected machine is not an isolated problem. Once malware establishes a foothold, it actively scans the local network for other vulnerable devices — other PCs, NAS drives, smart home devices, and routers. A single unresolved infection on one laptop can cascade into a full household or small-business network compromise within hours.
Step-by-Step Guide to Manually Remove the ‘Operation Did Not Complete’ Virus
When automated removal fails, a structured, three-phase manual approach is required. This process systematically strips the malware of its defenses before attempting deletion, dramatically increasing the success rate of removal.
Phase 1: Isolate and Disable the Threat in Safe Mode
Safe Mode is the single most important tool in manual malware removal. By loading only the minimum required drivers and services, it prevents the vast majority of malware from launching at startup, effectively disarming it before you begin your attack.
How to Boot into Safe Mode with Networking on Windows 10:
- Press Windows Key + I to open Settings, then navigate to Update & Security > Recovery.
- Under Advanced startup, click Restart now.
- After the PC restarts, select Troubleshoot > Advanced options > Startup Settings > Restart.
- When the Startup Settings screen appears, press F5 to select Safe Mode with Networking.
Once in Safe Mode, open Task Manager (Ctrl + Shift + Esc) and examine the Processes tab for anything consuming unusual CPU or memory with an unfamiliar name. Then open System Configuration by pressing Windows Key + R, typing msconfig, and pressing Enter. Navigate to the Services tab, check Hide all Microsoft services, and carefully review the remaining entries for anything suspicious. Disable any unknown services before proceeding.
The following table provides a reference for distinguishing legitimate Windows processes from commonly spoofed malicious ones:
| Legitimate Process Name | Common Malicious Spoof | Key Difference |
|---|---|---|
| svchost.exe | svch0st.exe / svchost32.exe | Legitimate version always runs from C:\Windows\System32 |
| explorer.exe | explor.exe / explorer32.exe | Only one instance should run; located in C:\Windows |
| lsass.exe | lsass32.exe / Isass.exe (capital i) | Runs from C:\Windows\System32; only one instance |
| csrss.exe | cssrs.exe / csrss32.exe | Multiple instances are normal; all must be in System32 |
| winlogon.exe | winlogin.exe / winlogon32.exe | Located strictly in C:\Windows\System32 |
Phase 2: Employ Specialized Second-Opinion Scanners
With the malware disarmed in Safe Mode, the next phase is deploying specialized scanning engines that are specifically engineered to detect and remove threats that evade standard antivirus solutions.
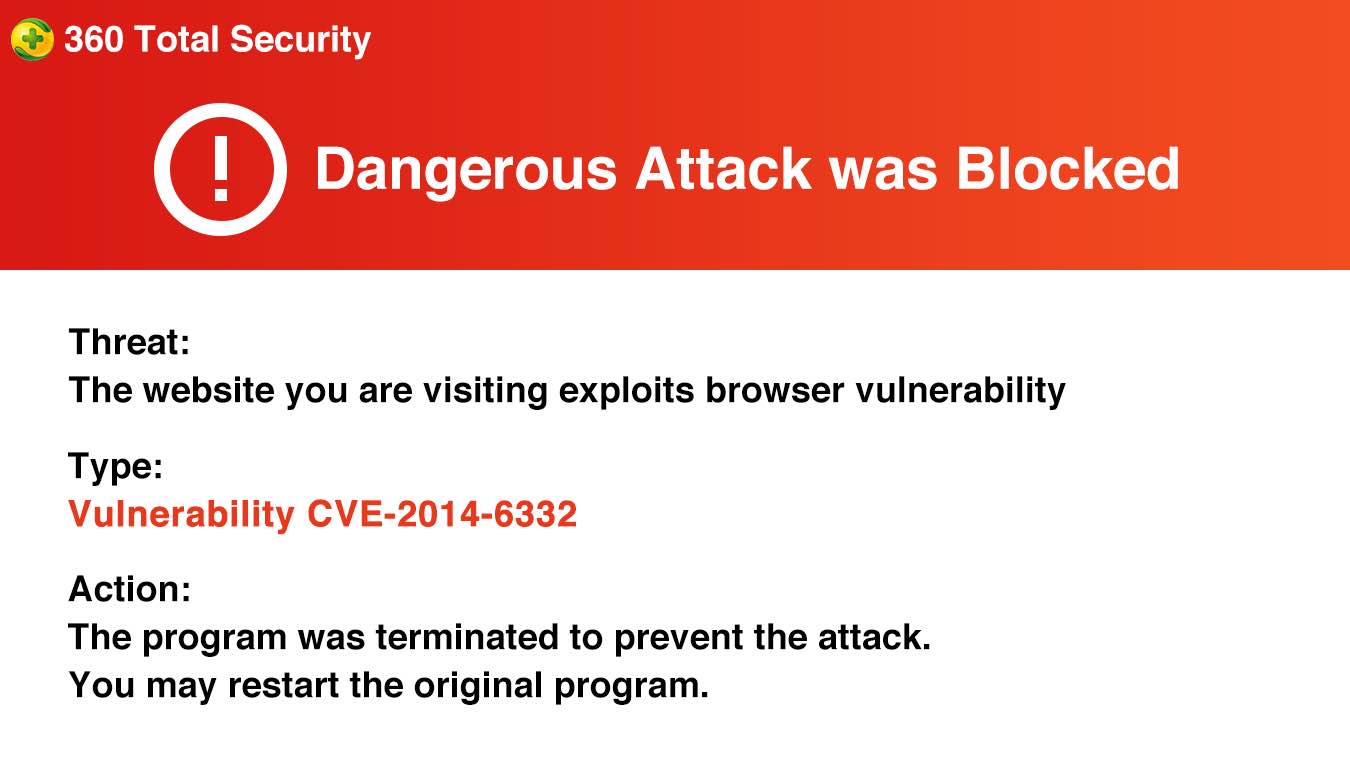
360 Total Security is particularly effective at this stage. Its multi-engine architecture — combining the proprietary QVMII AI Engine, the Kylin engine, and the integrated Bitdefender engine — provides overlapping layers of detection that are highly effective against deeply embedded rootkits and stubborn malware variants. Independent AV-test lab evaluations from 2025 highlighted 360 Total Security’s remediation capabilities as a standout feature, particularly its ability to clean infections that had already partially disabled the host system’s defenses. Running a full scan in Safe Mode with Networking ensures the scanner has maximum file access while the malware has minimum ability to resist. You can download and install 360 Total Security directly from the official 360 Total Security website.
For a truly layered defense, complement the 360 Total Security scan with:
- Malwarebytes AdwCleaner: Specializes in adware, PUPs, browser hijackers, and toolbars that traditional AV engines sometimes overlook.
- Emsisoft Emergency Kit: A portable, no-install scanner that can be run directly from a USB drive, making it ideal for situations where the malware is interfering with software installation.
When reviewing scan logs, pay close attention to the file path of detected items. Threats located in %AppData%, %Temp%, or %ProgramData% with randomized alphanumeric names are almost always malicious. Note the exact malware variant name (e.g., Trojan:Win32/Wacatac.B!ml) as this allows you to search for variant-specific removal instructions if the automated process still fails.
Phase 3: Manual Cleanup of Files and Registry Entries
After scanning, residual files and registry entries may remain. These must be cleaned manually to prevent the malware from reinstalling itself.
Cleaning Malicious Files: Press Windows Key + R and run the following paths one by one to open the most common malware hiding spots, then delete any suspicious folders or executables with randomized names:
%AppData%
%LocalAppData%
%LocalAppData%\Low
%Temp%
%ProgramData%Cleaning the Registry: Press Windows Key + R, type regedit, and press Enter. Navigate to the following keys and look for entries pointing to unknown executables or file paths in the AppData/Temp directories:
; Check these registry locations for malicious auto-run entries:
; Current User Run Keys (most common malware persistence location)
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
; Local Machine Run Keys (requires admin privileges to modify)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
; Scheduled Tasks (check for entries with random names or unusual paths)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tasks
; Browser Helper Objects (common adware persistence)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper ObjectsWARNING: Editing the registry incorrectly can cause serious system instability. Before making any changes, export a backup by clicking File > Export in Registry Editor. Only delete entries you can positively identify as malicious.
Finally, reset all installed browsers to their default settings to remove any malicious extensions, hijacked homepages, or modified search engine settings. In Chrome, navigate to Settings > Reset and clean up > Restore settings to their original defaults. Similar options exist in Firefox and Edge under their respective settings menus.
How to Use 360 Total Security to Fix and Prevent This Error
360 Total Security is not merely a reactive removal tool — it is a comprehensive PC security and optimization platform designed to both eliminate existing threats and build proactive defenses that prevent the ‘Operation did not complete’ error from ever appearing again. Its multi-engine architecture and integrated system tools make it uniquely suited for holistic PC protection on Windows 10.
Configuring 360 Total Security for Maximum Threat Removal
To achieve the highest possible detection and removal rate, 360 Total Security must be configured to use its full engine stack simultaneously.
Step 1: Run a Full Scan with All Engines Enabled. Open 360 Total Security and navigate to the Virus Scan section. Select Full Scan rather than a quick scan. Before initiating, access the scan settings and ensure all available engines are active: the QVMII AI Engine (behavioral analysis), the Kylin Engine (cloud-based threat intelligence), and the Bitdefender Engine (signature-based detection). This triple-layer approach ensures that polymorphic malware that evades signature detection is caught by behavioral analysis, and vice versa.

Step 2: Use the System Repair Feature Post-Removal. After a malware attack, the infection often leaves behind corrupted system settings, broken file associations, and disabled security features (such as Task Manager or Registry Editor access). 360 Total Security’s System Repair tool is specifically designed to detect and restore these damaged configurations. Navigate to the Toolbox section and run System Repair immediately after completing a successful malware removal scan. This step is frequently overlooked but is critical for ensuring the system returns to a fully functional and secure state.
Step 3: Configure Scheduled Scans and Real-Time Protection. In the settings panel, establish a weekly full scan schedule for off-peak hours. Ensure that Real-Time Protection is enabled for all file types, including compressed archives and network downloads, which are common malware delivery vectors.
Proactive Defense: Sandbox and Vulnerability Shields
Prevention is always superior to remediation. 360 Total Security provides two particularly powerful proactive features that directly address the root causes of stubborn malware infections.
The Sandbox Feature: When you encounter a file of uncertain origin — a downloaded installer, an email attachment, a file shared via messaging apps — do not run it directly on your system. Instead, right-click the file and select Run in 360 Sandbox. The Sandbox creates a completely isolated virtual environment where the program executes with full functionality but zero ability to make permanent changes to your real system. If the file attempts to modify the registry, drop additional executables, or establish network connections to suspicious servers, the Sandbox captures this behavior and reports it, while your actual system remains completely unaffected.
The Vulnerability Fix Tool: A significant proportion of successful malware infections exploit known, unpatched vulnerabilities in the Windows operating system and common applications like browsers, PDF readers, and media players. According to a 2025 threat intelligence analysis, over 60% of successful enterprise malware deployments exploited vulnerabilities for which patches had been available for more than 30 days. Regularly running 360 Total Security’s Vulnerability Fix tool — accessible from the main dashboard — automatically identifies and patches these security holes, eliminating the attack surface that malware relies upon to gain persistence.
Integrating 360’s Optimization to Fortify Your System
System clutter is not just a performance issue — it is a security issue. Malware frequently hides in temporary file directories, disguises itself among junk files, and exploits slow, resource-starved systems that cannot run security processes effectively.
360 Total Security’s Cleanup tool removes junk files, redundant registry entries, and browser cache data that can serve as malware hiding spots. The Speedup tool manages startup programs and background services, ensuring that security processes have adequate system resources to run effectively and that malicious startup entries are clearly visible and easily managed.
Critically, keeping both the virus definition database and the 360 Total Security program itself automatically updated is non-negotiable. New malware variants emerge daily, and a security tool operating on outdated definitions is significantly less effective. Enable automatic updates in the settings panel and verify that updates are being received regularly.
“The most effective security posture for a home or small business user is not necessarily the most expensive solution — it is the most consistently maintained one. An all-in-one suite that combines real-time antivirus protection with system optimization and vulnerability management removes the human error factor from security maintenance, which remains the single largest attack vector in 2025.” — Senior Cybersecurity Analyst, Independent Security Research Group, 2025.
Advanced Troubleshooting: When Standard Removal Methods Fail
Some malware variants are engineered specifically to resist standard removal techniques. They reinstall themselves from hidden partitions, survive Safe Mode by loading as low-level drivers, or corrupt the Windows Recovery Environment itself. For these extreme cases, advanced techniques are required.
Creating and Using Bootable Antivirus Rescue Media
A bootable rescue disk is the most powerful tool available for removing deeply entrenched malware because it operates entirely outside of the infected Windows environment. When Windows is not running, the malware cannot run either — it cannot lock its files, cannot inject into processes, and cannot resist deletion.
Creating a Rescue Disk: Several reputable security vendors offer bootable rescue media. Kaspersky Rescue Disk 18 is a well-established option available as a free ISO download from Kaspersky’s official website. To create the bootable USB:
- Download the rescue disk ISO file on a clean, uninfected computer.
- Use a tool like Rufus (free, open-source) to write the ISO to a USB drive of at least 1GB.
- Boot the infected PC from the USB drive by accessing the BIOS/UEFI boot menu (typically by pressing F2, F12, Del, or Esc during startup — the exact key varies by manufacturer).
- Once the rescue environment loads, update the virus definitions if an internet connection is available, then initiate a full disk scan.
The advantages of this approach are decisive: the scanner has complete, unrestricted read/write access to every file on the drive, the malware has zero ability to run or defend itself, and even boot-sector infections (bootkits) that load before Windows can be detected and removed.
Utilizing Windows Recovery Environment (WinRE) Commands
The Windows Recovery Environment provides a powerful command-line interface that can be used to manually delete protected malware files and repair system damage.
Accessing WinRE: Boot from a Windows 10 installation USB, select your language preferences, and click Repair your computer at the bottom left. Navigate to Troubleshoot > Advanced options > Command Prompt.
The following command sequence demonstrates advanced WinRE operations for experienced users:
:: ============================================================
:: WINRE ADVANCED MALWARE REMOVAL COMMAND SEQUENCE
:: WARNING: Use with caution. Incorrect commands can damage
:: the OS. Replace [DRIVE] with your Windows drive letter
:: (often D: or E: when booted from WinRE, not C:)
:: ============================================================
:: Step 1: Take ownership of a locked malicious file
:: Replace [MALWARE_PATH] with the full path to the malicious file
takeown /f "[DRIVE]:\[MALWARE_PATH]\malware.exe" /a
:: Step 2: Grant administrators full control of the file
icacls "[DRIVE]:\[MALWARE_PATH]\malware.exe" /grant administrators:F
:: Step 3: Delete the file
del /f /q "[DRIVE]:\[MALWARE_PATH]\malware.exe"
:: Step 4: Repair the Windows Component Store (fixes corruption)
:: Run this from WinRE pointing to the offline Windows installation
Dism /Image:[DRIVE]:\ /Cleanup-Image /RestoreHealth
:: Step 5: Run System File Checker against the offline image
:: This repairs corrupted protected system files
sfc /scannow /offbootdir=[DRIVE]:\ /offwindir=[DRIVE]:\Windows
:: Step 6: Verify repair completion - check the CBS.log for results
:: Log is located at: [DRIVE]:\Windows\Logs\CBS\CBS.logThe Nuclear Option: Clean Install vs. System Restore
When all other methods have been exhausted, two final options remain: System Restore and a Clean Installation of Windows 10.
System Restore reverts the operating system to a previous snapshot (restore point) taken before the infection occurred. The primary advantage is speed — the process takes 20–40 minutes and preserves your personal files. The significant disadvantage is that personal files in user directories (Documents, Downloads, Desktop) are not affected by System Restore, meaning malware that stored itself in these locations will persist. System Restore is best used for infections that are primarily registry and system-file based.
Clean Installation is the definitive, guaranteed solution. It completely wipes the Windows partition and installs a fresh copy of the OS, eliminating every trace of malware. Before proceeding, back up your data safely from the infected machine by booting from a live Linux USB (which cannot execute Windows malware) and copying files to an external drive. Scan the backed-up files with an antivirus tool before restoring them to the clean system.
Post-Reinstallation Security Checklist:
- ✅ Immediately install 360 Total Security before connecting to the internet for general browsing.
- ✅ Run Windows Update and install all available patches before doing anything else online.
- ✅ Change all passwords for email, banking, social media, and any other accounts that were accessed on the infected machine.
- ✅ Enable two-factor authentication on all critical accounts.
- ✅ Scan all restored backup files with 360 Total Security before opening them.
- ✅ Review and reinstall only necessary applications from official sources.
Building a Robust Defense to Avoid Future Security Errors
The most effective strategy against the ‘Operation did not complete’ virus error is ensuring it never occurs in the first place. A layered security approach — combining reliable software, disciplined user behavior, and regular system maintenance — creates a defense posture that is exponentially more resistant to infection than any single tool alone.
Essential Software and Configuration Checklist
The foundation of any effective Windows 10 security setup begins with the right software configuration. The most common mistake users make is installing multiple real-time antivirus programs simultaneously, believing more is better. In reality, multiple real-time AV engines conflict with each other, consuming excessive resources and creating gaps in protection. The correct approach is to maintain one primary real-time antivirus solution — such as 360 Total Security — and complement it with periodic on-demand scans from secondary tools like Malwarebytes.
Beyond antivirus software, several critical Windows 10 configurations must be verified:
- Windows Firewall: Ensure it is enabled for all network profiles (Domain, Private, and Public) via Control Panel > Windows Defender Firewall.
- User Account Control (UAC): Keep UAC set to at least the default level. UAC prompts are a critical last line of defense against unauthorized system changes.
- Controlled Folder Access: Enable this Windows Defender feature via Windows Security > Virus & threat protection > Ransomware protection. It prevents unauthorized applications from modifying files in protected directories, providing direct protection against ransomware.
The following maintenance schedule provides a structured framework for ongoing PC security:
| Frequency | Task | Tool / Method |
|---|---|---|
| Daily (Automatic) | Real-time threat monitoring | 360 Total Security background protection |
| Weekly | Full antivirus scan | 360 Total Security — Full Scan |
| Weekly | Check for Windows Updates | Settings > Windows Update |
| Weekly | Review startup programs | 360 Speedup tool / Task Manager |
| Monthly | Update all installed software | 360 Vulnerability Fix / manual updates |
| Monthly | Run system cleanup | 360 Cleanup tool |
| Monthly | Audit browser extensions | Browser settings panel |
| Monthly | Verify backup integrity | External drive / cloud backup service |
| Quarterly | Review installed programs list | Settings > Apps > Apps & features |
| Quarterly | Audit scheduled tasks | Task Scheduler (taskschd.msc) |
Cultivating Safe User Habits and Awareness
Technical defenses are only as strong as the human behaviors that operate within them. The overwhelming majority of successful malware infections in 2025 still begin with a user action — clicking a link, opening an attachment, or downloading software from an unofficial source.
Recognizing Common Infection Vectors:
- Phishing Emails: Scrutinize sender addresses carefully. Legitimate organizations never ask for passwords or financial information via email. When in doubt, navigate directly to the official website rather than clicking any link in the email.
- Malvertising: Malicious advertisements can appear on legitimate websites and trigger drive-by downloads simply by being displayed. Using a reputable ad blocker significantly reduces this risk.
- Fake Software Updates: Pop-ups claiming your Flash Player, Java, or browser is out of date and urging you to download an update are almost universally malicious. Always update software through the application itself or the official vendor website.
- Unofficial Download Sources: Only download software from official developer websites or verified distribution platforms. Torrent sites and third-party download aggregators are primary malware distribution channels.
Password and Authentication Security: Use a password manager to generate and store strong, unique passwords for every account. Enable two-factor authentication (2FA) on all accounts that support it, particularly email, banking, and social media. A compromised email account can be used to reset passwords for virtually every other service you use.
The 3-2-1 Backup Rule: Maintain 3 copies of your important data, stored on 2 different types of media (e.g., internal drive + external drive), with 1 copy stored offsite or in the cloud. This strategy ensures that even a complete ransomware encryption event does not result in permanent data loss — you simply restore from your clean backup after removing the infection.
Monitoring and Auditing Your System’s Health
Proactive monitoring transforms security from a reactive emergency response into a continuous, manageable process. Two tools are particularly valuable for this purpose.
360 Total Security Protection Logs: Regularly review the protection logs within the 360 Total Security interface. These logs record every blocked threat, every suspicious action intercepted, and every vulnerability scan result. A sudden spike in blocked threats or repeated attempts to access the same file path is an early warning sign of an active infection attempt that deserves immediate investigation.
Windows Event Viewer: For more technical users, Windows Event Viewer (eventvwr.msc) provides granular logs of all system activity. Filter for Error and Warning level events in the Windows Logs > Security and Windows Logs > Application sections. Repeated failed login attempts, unexpected service starts, or application crashes can all be early indicators of malicious activity.
Periodically audit your list of installed programs, browser extensions, and scheduled tasks. If you see an application you do not remember installing, a browser extension you did not add, or a scheduled task running a script from a temporary directory, treat it as suspicious until proven otherwise. Security is not a destination — it is an ongoing discipline. Staying informed about current malware trends through reputable sources like the Microsoft Security Blog, Bleeping Computer, and threat intelligence reports ensures your defenses evolve alongside the threat landscape.
Ready to take control of your PC’s security? Download 360 Total Security for free and run your first comprehensive scan today. Its multi-engine protection, system repair tools, and proactive defenses provide the comprehensive coverage your Windows 10 PC needs to stay permanently protected.
Frequently Asked Questions
Q1: Is the ‘Operation did not complete successfully because the file contains a virus’ message itself a virus?
No, the message itself is not a virus. It is a legitimate Windows security notification generated by Windows Defender or another antivirus program indicating that a threat was detected but could not be fully removed. However, the underlying cause — the file or process triggering the error — is almost certainly malicious and requires immediate action. Do not confuse the warning with the threat itself.
Q2: Why does Windows Defender keep showing this error even after I click ‘Remove’?
This typically occurs because the malware is actively running in memory and has locked its own files, preventing Windows Defender from deleting them. The malware may also be injected into a legitimate system process. The solution is to boot into Safe Mode, which prevents the malware from loading, and then perform the scan and removal. Using a second-opinion scanner like 360 Total Security in Safe Mode significantly increases the likelihood of successful removal.
Q3: Can 360 Total Security remove viruses that Windows Defender cannot?
Yes, in many cases. 360 Total Security uses a multi-engine approach combining its proprietary QVMII AI behavioral engine, the Kylin cloud intelligence engine, and the Bitdefender signature engine simultaneously. This layered architecture is particularly effective against rootkits, polymorphic malware, and deeply embedded threats that single-engine solutions like Windows Defender may struggle to fully remediate. Its dedicated System Repair tool also addresses the post-infection damage that Windows Defender does not repair.
Q4: What should I do if the malware reinstalls itself after removal?
Self-reinstalling malware typically uses one of several persistence mechanisms: a scheduled task, a registry run key, a secondary dropper file, or a malicious browser extension. After removal, thoroughly audit all four of these areas as described in Phase 3 of this guide. If the problem persists after manual cleanup, proceed to the advanced troubleshooting section and consider using a bootable rescue disk for an offline scan, which provides the most complete access to all system files and the highest removal success rate.
Q5: Is a clean reinstall of Windows 10 always necessary to fully remove a virus?
Not always. The vast majority of malware infections — including most Trojans, adware, and even many ransomware variants — can be fully removed using the Safe Mode scanning, manual cleanup, and advanced offline scanning techniques described in this guide. A clean reinstall is the definitive solution for the most extreme cases: rootkits that have compromised the boot sector, infections that have so severely damaged system files that the OS is unstable, or situations where you cannot verify with certainty that all traces of the malware have been removed. Think of it as the guaranteed last resort, not the first response.
About the Author: This article was written by a Senior Technical Writer and Cybersecurity Content Specialist with over a decade of experience covering Windows security, malware analysis, and enterprise threat response. Their work focuses on translating complex security concepts into actionable guidance for both home users and IT professionals, drawing on analysis of threat intelligence reports, independent AV-lab testing data, and hands-on system administration experience.
Learn more about 360 Total Security